217 results for: phone
Transitioning from a Home Office to a Virtual Office
Category : Web marketing 08-03-2024 by Janeth Kent
The best and most amazing Alexa Hacks you should know about
Category : Operating systems 30-06-2023 by Janeth Kent
Google Play Games on PC: Transforming Your Gaming Experience
Category : Videogames 06-06-2023 by Janeth Kent
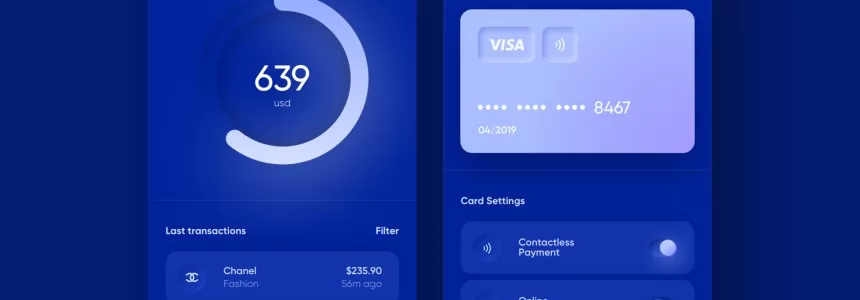
The Payment Request API: Revolutionizing Online Payments (Part 2)
Category : Javascript 08-06-2023 by Silvia Mazzetta
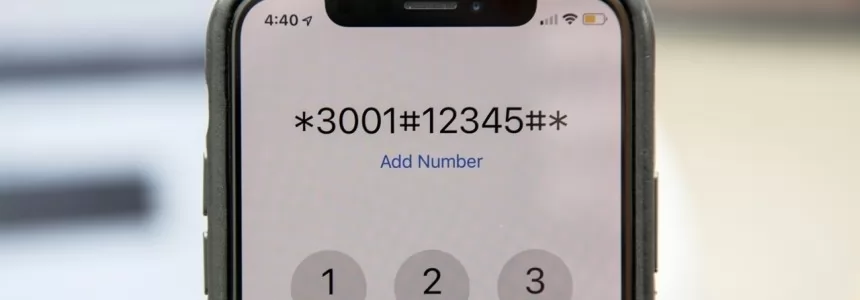
Android Hidden Codes: unveiling custom dialer codes and their functionality
Category : Mobile 02-06-2023 by Janeth Kent
How to download an email in PDF format in Gmail for Android
Category : Technology 16-05-2023 by Janeth Kent
The history of video games: from entertainment to virtual reality
Category : Videogames 28-11-2022 by Janeth Kent
Sick of Video Games? Here are Some Other Pastimes to Try
Category : Technology 29-11-2022 by Janeth Kent
8 benefits of having a website for your business
Category : Web marketing 03-06-2022 by Nadal Vicens
Advanced Android tutorial: discover all your phone's secrets
Category : Mobile 06-05-2021 by Janeth Kent
How to set up your Android phone: learn how to get your new phone up and running
Category : Mobile 28-04-2021 by Janeth Kent
5 Terrific iOS-Friendly Canva Alternatives to Upgrade Your Marketing Visuals
Category : Web marketing 05-05-2021 by Janeth Kent
Parental controls on Android: how to make mobiles and tablets child-friendly
Category : Security 26-04-2021 by Janeth Kent
How to hide the you are typing text in a WhatsApp group
Category : Social networks 25-03-2021 by Janeth Kent
Top Graphic Design e-Books & How to Get them on Your iDevice
Category : Ui/ux design 03-03-2021 by Luigi Nori
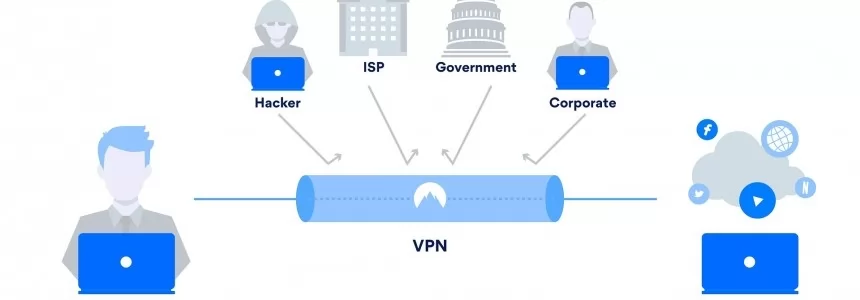
Cybersecurity and Data Privacy: Why It Is So Important
Category : Security 26-02-2021 by Janeth Kent
Interesting and Helpful Google Search Features You’ll Want to Start Using
Category : Software 31-01-2021 by Iveta Karailievova
How to have two WhatsApp accounts on your Dual SIM phone
Category : Software 25-01-2021 by Luigi Nori
Understanding LCP, CLS, FID. All about Core Web Vitals in Google Search Console
Category : Seo & sem 14-01-2021 by
How to use your browser as a file browser, in Chrome or Microsoft Edge
Category : Technology 26-12-2020 by Janeth Kent
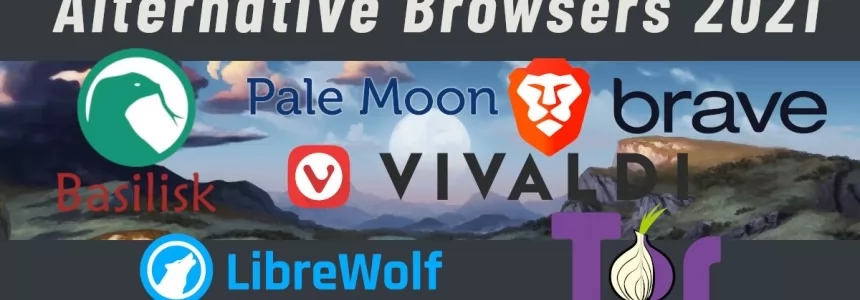
Some Neat Ways to Improve Your Internet Browsing Experience?
Category : News and events 21-12-2020 by Janeth Kent
The BleedingTooth vulnerability and other Bluetooth security risks
Category : Security 10-11-2020 by Iveta Karailievova
The best tricks and features to master your Android Smart TV
Category : Networking 05-11-2020 by Luigi Nori
What's the Difference between Google TV and Android TV?
Category : Software 27-10-2020 by Silvia Mazzetta
How to prevent your neighbor from hacking your Chromecast
Category : Networking 26-10-2020 by Luigi Nori
3 awesome ways technology is helping us combat the COVID pandemic
Category : Technology 28-10-2020 by Iveta Karailievova
How to turn an Android device into a retro game console
Category : Software 14-10-2020 by Silvia Mazzetta
Data Scraping and Data Crawling, what are they for?
Category : Web marketing 25-09-2020 by Silvia Mazzetta
How to securely access the Dark Web in 15 steps. Second part
Category : Security 08-03-2024 by Janeth Kent
Suggestions to Improve the Efficiency of a Small Business
Category : Web marketing 26-07-2025 by Janeth Kent
How to securely access the Dark Web in 15 steps. First part
Category : Security 08-03-2024 by Silvia Mazzetta
Free Netflix: everything you can see without subscribing
Category : News and events 09-09-2020 by Luigi Nori
How to setup an Android TV with androidtv.com/setup or the Google application
Category : Operating systems 26-10-2020 by Janeth Kent
What cybersecurity professionals have learned from the lockdown experience
Category : Security 26-08-2020 by Silvia Mazzetta
Browse safely and privately from your mobile phone using a VPN
Category : Security 25-08-2020 by Janeth Kent
The 6 Essentials for Creating a Visually Appealing Web Design
Category : Web design 25-08-2020 by Silvia Mazzetta
How to configure Tor to browse the deep web safely
Category : Security 12-08-2020 by Silvia Mazzetta
How Learning Accents Connects Us To The World At Large
Category : Web marketing 16-07-2020 by Janeth Kent
Parenting, pandemic and UX: Learning from design of experiences
Category : Ui/ux design 17-06-2020 by Silvia Mazzetta
Neumorphism (aka neomorphism) : new trend in UI design
Category : Ui/ux design 17-06-2020 by Silvia Mazzetta
How to get notified when one of your WhatsApp contact is online
Category : Software 15-06-2020 by Silvia Mazzetta
How to turn your smartphone into a webcam for your pc
Category : Multimedia 17-05-2020 by Luigi Nori
First steps into JavaScript – a practical guide 3
Category : Javascript 07-05-2020 by Iveta Karailievova
What is Google My Business and how does it help my local business?
Category : Web marketing 02-05-2020 by Luigi Nori
Online Marketing Strategies for your Ecommerce
Category : Web marketing 20-04-2023 by Silvia Mazzetta
The best websites of the Tor Deep Web and Dark Web Network
Category : Security 03-11-2022 by Janeth Kent
How to find everything you need on the Deep Web and the Dark Web
Category : Security 10-05-2021 by Silvia Mazzetta
Best ways to start a video conference without registration
Category : Multimedia 21-04-2020 by Silvia Mazzetta
How They Can Hack You While Navigating: Protecting Your Digital Security
Category : Security 23-06-2023 by Silvia Mazzetta
Layouts with Bootstrap 4: how to create a responsive web
Category : Web design 23-11-2019 by Silvia Mazzetta