We have not learned and we still use passwords that are extremely easy to hack and vulnerable to cyber attacks. If you don't want your credentials to end up in the hands of criminals or traded on the dark digital shelves of the Deep Web, we bring you a simple guide to building (almost) unhackable passwords.
The first thing you need to make sure is that your password does not incur any obviousities, such as using sequential numbers or letters, birthday dates, first and last names or your pet. Passwords should be unique, unintelligible and not include personal information.
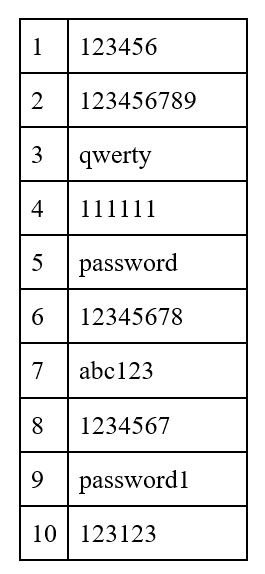
First of all, don't do things like this:
And when building your secure password, follow the guidelines listed below:
Length is key: This is, according to Avast, the most critical factor. No password should be shorter than 15 characters.
Use as complex a combination of characters as possible: The more you mix up letters (such as upper and lower case), numbers and symbols, the stronger and more robust the password will be and the harder it will be for a brute-force attack to crack it.
Avoid common substitutions: Password crackers are up to the usual substitutions. These days, random character placement is much more effective than common leetspeak * substitutions (* definition of leetspeak: an informal language or code used on the Internet, in which standard letters are often replaced by numbers or special characters).
Do not use keyboard paths: As with the previous tips, do not use sequential letters and numbers, nor sequential keyboard paths (such as qwerty).
Your password should never be a single word: Otherwise, it will be very easy to guess.
Use the revised sentence method: Select strange and unusual words including proper names, names of local businesses, historical figures, words in another language, or exotic animals. Make a mental picture of the concepts and incorporate random characters in between to increase the level of complexity.
Use the Bruce Schneier Method: The idea is to think of a random sentence and turn it into a password using a ruler. For example, take the first two letters of each word.
Muscle memory method: Valid only for some people, in this technique your fingers remember instead of your brain. You can use a random password generator, memorize it as phonetically as possible and type it several times on the keyboard until it is in your muscle memory.
Periodically check if your passwords are part of some massive data gap.
Opt for two-factor authentication (2FA) and multi-factor authentication (MFA) to add an extra layer of protection. This could be a code sent to your phone, biometric data such as a fingerprint or eye scan, or a physical token.
Security Keys: A security key like the YubiKey provides the most advanced protection available today. It serves as your MFA, giving you access to files only if you physically have the key. Security keys are available in USB, NFC or Bluetooth versions, and are generally the size of a USB memory stick.
Use a VPN to connect to public Wi-Fi. That way, when you log in to your accounts, no one intercepts your username and password.
Of course, never send a text message or email to anyone with your password.
When you select security questions when creating an account, choose options that are hard to predict and only you know the answer, not solutions that are easy to find on your social networks.

