results for: free
Network attacks and how to avoid them
Nowadays it is impossible to list all the different types of attacks that can be carried out on a network, as in the world of security this varies continuously. We bring you the most common ones according to the network attack databases, so that we can keep up to date…
Category : Security 03-05-2021 by Silvia Mazzetta
Use the SRCSET attribute to improve your SEO
There is a new standard HTML attribute that can be used in conjunction with IMG called SRCSET. It is new and important as it allows webmasters to display different images based on the size of the device, and without using javascript or other special code. This means we can serve…
Category : Web design 21-03-2024 by Silvia Mazzetta
5 Terrific iOS-Friendly Canva Alternatives to Upgrade Your Marketing Visuals
Sometimes you want to use your iPhone to create compelling, engaging marketing visuals, and as awesome as Canva is, many of us are interested in seeing what other options are out there. As all marketers know, consistent branding is a must for any company (or even individual) who wants to stand…
Category : Web marketing 05-05-2021 by Janeth Kent
How to improve customer experience through speech recognition
Voice of the Customer (VoC) is essential to a successful customer experience (CX) programme. However, VoC data is often disparate, making it difficult to use. Service organisations looking to make more informed decisions about customer experience (CX) investments and improvements should implement a consistent voice of the user (VoC) strategy,…
Category : Technology 27-04-2021 by Janeth Kent
eSports streaming market breaks all records
If it was already very successful globally before, in the wake of the pandemic the online game streaming industry has managed to grow to totally unexpected levels. Its expansion is unstoppable and experts predict that its value will grow by 70% in the next four years and could reach some…
Category : Videogames 27-04-2021 by Janeth Kent
Parental controls on Android: how to make mobiles and tablets child-friendly
Despite all the good things about them, mobile devices can expose your children to content that they're better off not seeing. The good news is that your Android phone or tablet comes with built-in tools that can help you ensure your kids can only access age-appropriate content and, as we'll…
Category : Security 26-04-2021 by Janeth Kent
Top tools for UX design and research
This article is a compilation of the "ux tools" I have tested in recent years. I've separated the tools by categories, although I recommend you to take a look at all of them, you might find some you didn't know. - Conceptualisation and project management tools - UX testing and research tools - Analytics…
Category : Ui/ux design 23-04-2021 by Silvia Mazzetta
The best free tools to Transcribe audio to text
With this article we bring you a list of the best tools for transcribing audio to text, offering you some that simply do it with dictated audio, but also others capable of loading audio files. The collection is varied, and we have mobile applications, web pages, and computer programs capable…
Category : Software 15-04-2021 by Janeth Kent
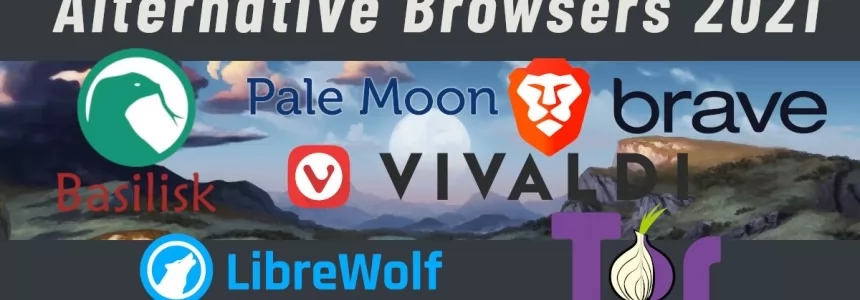
6 Best Alternative Privacy Focused Browsers in 2021
In today's article we take a look at free private browsers which are relevant in 2021. We will compare their advantages and disadvantages, specs, etc. Let's get into it. What are alternative browsers? Alternative browsers are mostly trying to increase browser security, by various methods, such as browser hardening, sandboxing, encryption forcing, etc. When…
Category : Software 22-04-2021 by
Bootstrap 5 beta2. What offers?
Since the release of the Bootstrap 4 is three years, in this article we will present what is new in the world’s most popular framework for building responsive, mobile-first sites. If you want to know what are the significant changes that come with the next version 5 which is in…
Category : Css 05-04-2021 by
Top Graphic Design e-Books & How to Get them on Your iDevice
Ma-no.org may include links to commercial websites. A commercial website is defined as a business site designed to generate income through the provision of services and products. Where links to commercial sites are included on ma-no.org, this does not indicate or imply any affiliation or endorsement between that commercial entity…
Category : Ui/ux design 03-03-2021 by Luigi Nori
Cybersecurity and Data Privacy: Why It Is So Important
The internet has made it very easy for people all across the world to stay connected with one another. Access to information, services, and people is possible for pretty much anyone with an internet connection today. But while this has brought many positive changes to how people live and connect,…
Category : Security 26-02-2021 by Janeth Kent
Top 7 Potential Tools for Automation Testing
Today's digital economy has significantly changed how organizations deliver products and services. Many organizations are gravitating towards smart methodologies and automated tools to spark customer interest in their products and increase revenue to ensure quality and speedy deliveries. These testing tools help organizations to determine the expected and actual product delivery…
Category : Web marketing 12-02-2021 by Janeth Kent
Graphic design and its impact on Web Development
In today's article we will explain the concept of graphic design, its fundamentals and what it brings into web development. Graphic design is applied to everything visual, believe or not, it can aid in selling a product or idea, it's applied company identity as logos, colors, typography of the company…
Category : Web design 05-04-2021 by
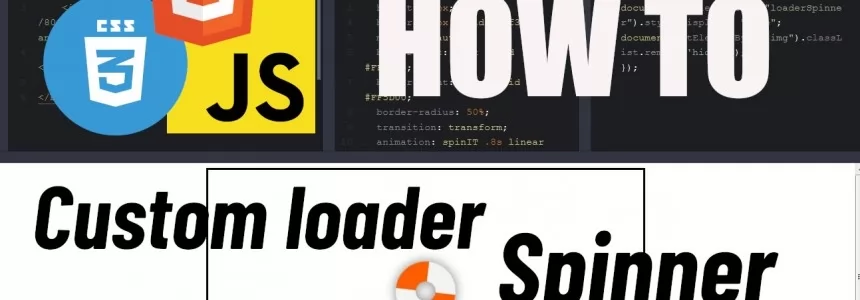
Creating simple CSS spinner-loader
In today's article we will show you how to animate a basic loader that spins when some predefined action is defined, such as loading an image. That can be used on a website for example when there is a request running and the result is not yet retrieved. What are they? Loading…
Category : Css 05-04-2021 by
Top Whatsapp alternatives in 2021
From the communication platform WhatsApp leaves more and more users for different reasons. If you're one of them, there are a lot of possibilities on how to replace it with something better. We will show you what are the 5 free alternatives to WhatsApp to have a text or audio-video conversation…
Category : Software 26-01-2021 by
How to have two WhatsApp accounts on your Dual SIM phone
Having two WhatsApp accounts on the same Android or iOS cell phone is possible. To do this, your terminal must be a phone with Dual SIM compatibility, that is, by allowing you to have two numbers on it, you could have two WhatsApp accounts on it. For example, this is useful…
Category : Software 25-01-2021 by Luigi Nori
Read comics online: best websites and apps to download and read digital comics
Comic book lovers (like us), today we're going to give you a special tribute: a small collection of websites and applications to download and read digital comics, both on your computer and on your mobile devices. You'll be able to access a wide collection of free and paid digital comics, and…
Category : News and events 26-05-2023 by Silvia Mazzetta
What is Django and what is it used for
When we talk about Django, we refer to that framework that is used for any totally free and open source web application which is written in Python. Basically, it's a group of elements that will help you create web pages much more easily and quickly. At the moment you are going…
Category : Programming 26-12-2020 by Janeth Kent
How to use your browser as a file browser, in Chrome or Microsoft Edge
We're going to explain how to use the Chrome browser as a file browser, both on Android and on your computer. This is a hidden feature of Chromium that will allow you to browse through the internal folders of your PC or mobile phone without needing any specific application to…
Category : Technology 26-12-2020 by Janeth Kent
The best free tools for linkbuilding
Linkbuilding is one of the main factors in improving the SEO positioning of a page. Having a profile of inbound links from pages with great authority can mean the difference between appearing at the top of the search engine or not. However, practicing linkbuilding, both in text and images, is one…
Category : Seo & sem 23-12-2020 by Janeth Kent
How to get paid in Bitcoin: CoinBase, CoinGate
After explaining how bitcoins work and how to pay using this cryptocurrency, we will see how to get paid in bitcoin. Below you will find explained in detail how to do it. Many people find the concept of BitCoin virtual currency confusing. We could simply explain that BitCoin is a peer-to-peer financial…
Category : Technology 23-12-2020 by Silvia Mazzetta
Dark Web: the creepy side of the Internet is not as dark as believed
People who surf the Dark Web are not necessarily looking for something illegal. Most people want to protect their privacy. And according to a recent study, 93 percent only use websites that are freely accessible. It is almost impossible not to leave traces on the Internet and therefore reveal a lot…
Category : Security 17-05-2023 by Silvia Mazzetta
Cross cultural challenges in web design, an overview
The user experience design of a product essentially lies between the intentions of the product and the characteristics of your user. - David Kadavy - The task of building a culturally appropriate website for a new market can be challenging: in this article we are going to talk about the impact of national…
Category : Web design 21-12-2020 by Maria Antonietta Marino
How to pay in Bitcoin: Hype and Coinbase
Once the wallet is created, let's see how to pay in Bitcoin to buy various products and services. If you have opened a Bitcoin wallet with HYPE, you can send payments using this cryptocurrency very easily. All you need to do is go to the Menu section of the HYPE app, press…
Category : Technology 10-12-2020 by Silvia Mazzetta
How to Use Bitcoin: mining, wallets, payments
You have certainly heard of Bitcoin, the virtual currency that periodically makes people talk about itself because of its innovative and particular nature. In this case, you have probably also wondered how it is possible to get and subsequently spend Bitcoins, and if it is something useful, as well as…
Category : Technology 10-12-2020 by Silvia Mazzetta
Security of Internet providers: can we trust it?
This year has been a time of many changes. Now, more people are connected to the Internet through their home routers for teleworking, shopping, or leisure. This is where the security of Internet operators becomes more important. The question is whether the ISP's security is good enough to be the only…
Category : Security 29-05-2023 by Janeth Kent
5 Tips to Bring More Traffic to Your Blog
Publishing a blog on your business website is an effective marketing tool for several reasons. Blog posts are the ideal place to share information about your company, products, services, and showcase your expertise or comment on industry trends. Blog posts also give you a space to express more personality, a sense…
Category : Seo & sem 03-12-2020 by Janeth Kent
Brief History of Biometric Authentication
These days, biometric authentication seems to be part of every little gadget or device we use. You’ve no doubt used it when logging onto your laptop, your tablet, or your cell phone, alongside more ‘old school’ methods like a password or PIN. Governments often use biometric authentication for security access and…
Category : Security 30-11-2020 by Janeth Kent
A beginner’s guide to software vulnerabilities
What are software vulnerabilities The number of devices connected to the Internet is growing every day. And among those devices we find not only computers and smartphones, but also an ever-rising number of cameras, smoke detectors, motion sensors, smart door locks, and let’s not forget that even plant pots. Many households…
Category : Security 17-11-2020 by Iveta Karailievova
The BleedingTooth vulnerability and other Bluetooth security risks
Have you ever heard of BleedingTooth? And we do not mean the really disturbing looking mushroom which goes by this name and is totally real (we double checked) but one of the lately discovered vulnerabilities in Linux systems. It had hit the tech news recently, when Andy Nguyen, a Google security…
Category : Security 10-11-2020 by Iveta Karailievova
The best tricks and features to master your Android Smart TV
We bring you a collection of the best tricks to squeeze Android TV, the Google operating system designed for televisions. You can find it on smart televisions of some brands, but also on devices that you will connect to the TV. With all of them, you can use different types…
Category : Networking 05-11-2020 by Luigi Nori
Why You Should Hire Node.js Developer for Your Backend Development
When developers are building a new website, they mainly focus on both frontend and backend development. The frontend code helps create the interfaces through which the app interacts with the users while the back-end code interacts with the server to deliver data or content that is displayed to the website…
Category : Javascript 27-10-2020 by Luigi Nori
How to watch deleted or private Youtube videos
Today we are going to talk about the technique which you permit to be able to recover videos from Youtube that was deleted, made private or simply blocked by Youtube itself. With this trick you most of the time would do just that. How is this possible we will explain…
Category : Social networks 05-04-2021 by
3 awesome ways technology is helping us combat the COVID pandemic
Times are hard now, that humanity once more stumbled into a terrible pandemic. But in comparison to the poor folks back in 1918 when the Spanish flu was on wreaking havoc, nowadays we have the advantage of cutting edge technology on our side. Here’s a quick list of top three ways…
Category : Technology 28-10-2020 by Iveta Karailievova
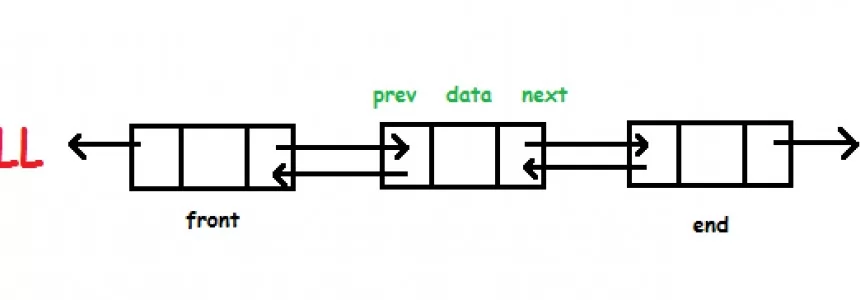
Hashmap: Overflow Lists
In this short series of articles we will go to see how it is possible to create the Hashmap data structure in C. In the implementation we're going to use the doubly concatenated lists as auxiliary data structures. Let's look at a possible implementation. Header file Let's first have a look to what…
Category : C language 18-06-2020 by Alessio Mungelli
MAME Multiple Arcade Machine Emulator: How to download and configure this arcade emulator for Windows
Despite the fact that new state-of-the-art computer games are coming out every so often, the whole retro theme is very appealing to users who are looking to relive the long hours spent in front of a console, such as the NES or SNES, and even in arcades playing arcade machines.…
Category : Software 14-10-2020 by Luigi Nori
How to turn an Android device into a retro game console
If you like retro games and you want to set up your own system at home, a good way to do it is using Android. From emulators for Mega Drive, N64, GBA, PS1 or Super Nintendo, to other systems such as MAME, all of them are available in Android app…
Category : Software 14-10-2020 by Silvia Mazzetta
Network and port scanning with Zenmap
This article goes out to all the computer nerds who are, when it comes to networking, more on the noob-side of the crowd. It does not have to be complicated and everyone with patience and eagerness to learn something new can relatively quickly gain the knowledge necessary to feel more…
Category : Security 08-10-2020 by Iveta Karailievova
HTTP Cookies: how they work and how to use them
Today we are going to write about the way to store data in a browser, why websites use cookies and how they work in detail. Continue reading to find out how to implement and manage them - if you're looking for code! Understanding HTTP COOKIES - What are they? Cookies and other types…
Category : Programming 27-11-2020 by
How to Unlock Secret Games in Chrome, Edge and Firefox
Your web browser is full of secrets. I usually spend a lot of time studying new features that I can unlock through pages like chrome://flags and about:config in the browser, but sometimes it's also fair and necessary to take a break and play the games that popular browsers hide. Yes, your…
Category : Videogames 07-10-2020 by Silvia Mazzetta
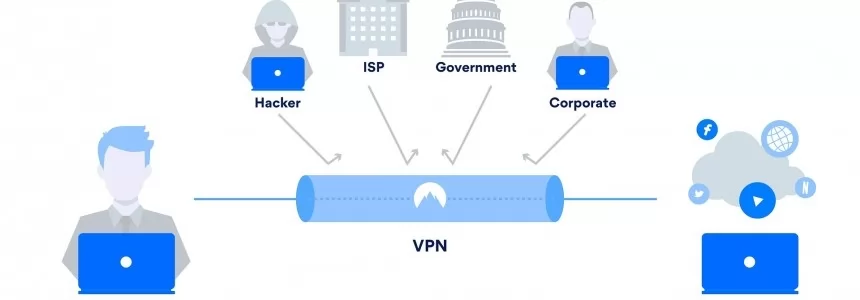
Double VPN: what it is and how it works
Privacy on the web is a very important factor for users and there are more and more tools to help us maintain it. Without a doubt VPN services have had a very important increase in recent times and represent an option to preserve our data when we browse. However, in…
Category : Security 28-09-2020 by Silvia Mazzetta
Data Scraping and Data Crawling, what are they for?
Right now we are in an era where big data has become very important. At this very moment, data is being collected from millions of individual users and companies. In this tutorial we will briefly explain big data, as well as talk in detail about web crawling and web scraping…
Category : Web marketing 25-09-2020 by Silvia Mazzetta
How to write our own Privacy Policy
In this article we will talk about Privacy Policy statements, how you can write one and implement it on your page. Why did it pop up? These days when we browse on any new page, or when we visit the site for the first time, most of the time we have to…
Category : Development 13-12-2023 by
How to securely access the Dark Web in 15 steps. Second part
Let's continue with the 2nd part of our article in which we try to give you some advice on how to safely and securely explore the dark web. Let's restart from number 6. 6. Changes the security level in the Tor browser It is also possible to increase the security level of the…
Category : Security 08-03-2024 by Janeth Kent
Suggestions to Improve the Efficiency of a Small Business
If you have a small business, it means that every resource matters. You have less room for error due to a lack of manpower as well as other aspects. So focusing on efficiency is something that ought to be your priority. Of course, inefficient experience is a big hindrance. You may…
Category : Web marketing 25-01-2022 by Janeth Kent
How to securely access the Dark Web in 15 steps. First part
The dark web can be a pretty dangerous place if you don't take the right precautions. You can stay relatively safe with a good antivirus and a decent VPN. However, if you want to be completely anonymous and protect your device, you'll need a little more than that. Here there are…
Category : Security 08-03-2024 by Silvia Mazzetta
How to Browse the Internet Anonymously: 6 tips
Most of the actions you take online are not as private as you might imagine. Nowadays, countless people and groups try to follow our online behaviour as closely as possible. Our ISPs, our network administrators, our browsers, search engines, the applications we have installed, social networks, governments, hackers and even the…
Category : Security 16-09-2020 by Silvia Mazzetta
Mobile cryptophones on the market (legals)
As we have said, it is a market often at the borders of legality, also because these devices are particularly used by criminals. Some models, however, are also available through standard commercial channels, while others are sold through direct distributors and cash payment. We list some of them here, with the…
Category : Security 15-09-2020 by Silvia Mazzetta
What is a Cryptophone and how it works
The so-called cryptophones, are anti-interception smartphones as they use encryption methods to protect all communication systems. Here are all the details and the truth about these "unassailable" phones. The recent Encrochat affair, recently investigated for illegal activities, has brought to light the so-called cryptophones. They are smartphones - legal in themselves -…
Category : Security 11-09-2020 by Silvia Mazzetta
Free Netflix: everything you can see without subscribing
To view the contents of an audiovisual streaming platform such as Netflix, it is necessary to pay a monthly connection fee. However, the company has enabled a series of contents that can be viewed "for free", without having to pay for them. To view Netflix's free contents it is not necessary…
Category : News and events 09-09-2020 by Luigi Nori
How to comply with Google's quality guidelines in 2020
Google provides a set of guidelines on what your website's content should look like in order to appear in search results. There are several categories within the Google guidelines: Webmaster Guidelines. General guidelines. Content-specific guidelines. Quality guidelines. In this article we will focus on the Quality guidelines. Quality guidelines, describe techniques whose use is prohibited and which,…
Category : Seo & sem 09-09-2020 by Silvia Mazzetta
How to install a Linux partition on a Windows 10 PC
In spite of a past we could say almost confronted, the approach between Windows and Linux is accelerating more and more, drawing a story closer to love than to hate. So much so that Windows 10 already offers support for Linux natively. Creating a subsystem is no longer penalized. A…
Category : Operating systems 06-09-2020 by Luigi Nori
How are businesses using artificial intelligence?
The term Artificial Intelligence (AI), "the intelligence of the machines", unifies two words that, a priori, could not be associated, since the term intelligence is attributed to the faculty of the mind to learn, to understand, to reason, to take decisions and to form a determined idea of the reality. How…
Category : News and events 21-06-2023 by Silvia Mazzetta
How to setup an Android TV with androidtv.com/setup or the Google application
Android TVs and players are a good investment if you want to have all the entertainment at your fingertips. However, they require an installation that, although simple, has several ways to run. We show you how to set up your Android TV without complications and in less than five minutes. Android…
Category : Operating systems 26-10-2020 by Janeth Kent
What cybersecurity professionals have learned from the lockdown experience
The COVID-19 pandemic has radically changed the rules of the game for most companies and individuals in a very short time; it has also changed the international computing universe. Sudden changes in people's habits as well as in business operations have altered some of the elements that characterize cyber-risk. And…
Category : Security 26-08-2020 by Silvia Mazzetta
Browse safely and privately from your mobile phone using a VPN
Every day our smartphones suffer attacks, viruses, malware and information theft. In this article you will be able to deduce if you need a VPN in your mobile phone to safely surf the Internet, to avoid possible attacks on public Wi-Fi networks and also to filter out advertising and malware…
Category : Security 25-08-2020 by Janeth Kent
Get ready for the future: What Does The Future Of SEO Look Like?
How will SEO change in 2030? There are various positions and assumptions that we can make about this so that you can think about the strategies to take when the future catches up with us. Anyone who works in SEO knows the great challenge of positioning a site on the web…
Category : Seo 19-08-2020 by Silvia Mazzetta
How to configure Tor to browse the deep web safely
Today we explain how to set up Tor to browse safely, and we'll share some links to safe sites on the deep web to get you started. Many already know that not everything on the Internet appears in Google, Yahoo, Bing or other search engines, and that accessing much of this…
Category : Security 12-08-2020 by Silvia Mazzetta
7 Killer Strategies to Increase Your Sales Funnel Conversion Rates
Have you been using online sales funnels to grow your business online but it hasn't really worked for you? There's something you are not doing right. Use these strategies to make your sales funnels convert better. We are living in a competitive digital era, and as an entrepreneur, you have to…
Category : Web marketing 23-07-2020 by Janeth Kent
Why is Website Performance Important for Online Businesses?
Your web is the site where most individuals will connect with your business. Your digital marketing processes will most probably send customers to your website. It might be to get information concerning your products and services, obtain contact information, or make purchases. Website performance, also known as web optimization, is a…
Category : Web marketing 24-07-2020 by Janeth Kent
Popular DNS Attacks and how to prevent them
DNS services are essential for web browsing. However, it is one of the most vulnerable to attacks. This guide will detail the most dangerous DNS attacks and some actions that will protect the network infrastructure. One of the reasons why DNS services have some susceptibility to attack is the UDP transport…
Category : Security 20-07-2020 by Silvia Mazzetta
How to recover an Instagram hacked account
You can't access your Instagram account. The cybercriminal who probably hacked your profile changed your password. Now what? What to do now? First try to stay calm: unfortunately these things can happen, but there is a solution to everything, and today we will explain how to solve this specific problem. In this…
Category : Social networks 16-07-2020 by Janeth Kent
Bank phishing by email: best way to prevent it
No one is safe from Pishing attacks, especially bank Phising. Large and small companies in all industries are being attacked repeatedly. Phishing is so popular with cybercriminals because it provides them with access to the most vulnerable part of any network: the end users. Bank Phishing is increasingly being used…
Category : Security 16-07-2020 by Silvia Mazzetta
7 Most Effective Ways to Make Money From Photography
Many people all over the world enjoy photography. At first, it may seem difficult to learn, but once you turn it into a hobby, then it becomes a pleasure rather than a difficulty. And the better you get with photography, the more you understand and want to invest in better…
Category : News and events 15-07-2020 by Janeth Kent
A collection of interesting networks and technology aiming at re-decentralizing the Internet
The decentralised web, or DWeb, could be a chance to take control of our data back from the big tech firms. So how does it work? Take a look at this collection of projects aimed to build a decentralized internet. Cloud BitDust - is decentralized, secure and anonymous on-line storage, where only…
Category : Networking 27-08-2020 by Janeth Kent
Awesome JavaScript Games and Js Software to create Games
Best sites js13kGames 2019 - Highlights from the js13kGames 2019 competition. js13kGames 2018 - 13 Games in ≤ 13kB of JavaScript. js13kGames 2017 - Build a game in 13kB or less with js13kGames. Adventure Triangle: Back To Home - You are lost in the cave. Try to get out and back to home. Sometimes it…
Category : Javascript 30-06-2020 by Janeth Kent
Parenting, pandemic and UX: Learning from design of experiences
After the quarantine, many of us have had to adapt our work and personal routines to the new remote paradigm. As a mother, I decided to share some things I've learned. We've been in total quarantine for weeks. Weeks in which we close the office and live and work in the 4…
Category : Ui/ux design 17-06-2020 by Silvia Mazzetta
Is JavaScript good for machine learning?
One of the things you always hear when you are talking to someone related to the M.L. world is that, one must learn Python because the vast majority of the major libraries are in that technology. You're probably right, but I chose JavaScript as the metal of my sword and…
Category : Javascript 16-06-2020 by Silvia Mazzetta
How to get notified when one of your WhatsApp contact is online
Privacy is one of the most important aspects among most users of the popular Facebook messaging application. So much so, that many settings have been included in WhatsApp itself to offer users the ability to display their profile picture, status, info, or the time they last connected to the application…
Category : Software 15-06-2020 by Silvia Mazzetta
Dark Web: how to access, risks and contents
You've probably heard of the Dark Web before, but do you really know what the Dark Web is, or what it consists of? Do you know its risks? Which users use the Dark Web? What content is published? Would you know how to access the Dark Web safely? If you are reading…
Category : Security 13-06-2020 by Silvia Mazzetta
Why do you vote the way you do in the age of misinformation and fake news?
In this context of the electoral campaign in which we are immersed, the 'political hoaxes' are becoming more relevant and it is expected that attacks to destabilize the parties and candidates in order to influence the electorate will increase. As recent examples, let's remember that disinformation campaigns influenced Trump to win…
Category : News and events 11-06-2020 by Silvia Mazzetta
What is Cyber Intelligence and how is it used?
What is Cyber-intelligence and what is it used for? This is a question that is usually asked by security, cyber-security and intelligence professionals. Cyber-intelligence is a hybrid concept between these three worlds and professional fields, and therefore it is an opportunity and a necessity to know what it is and what…
Category : Security 11-06-2020 by Silvia Mazzetta
How to move Chrome, Firefox or Edge cache to save space
Caching is a technique used by many programs to improve their performance, especially for applications that run over the Internet, such as streaming programs or web browsers. This technique consists of saving all or part of the information being processed in a directory so that, if we return to it,…
Category : News and events 04-06-2020 by Janeth Kent
How beneficial is React Native for developing a mobile app?
A substantial alternative of cross-platform app development is fully native development. If you follow the approach of native mobile app development such as react native development company in Bangalore, you will be able to create separate ones for both Android as well as iOS. The framework of React Native is…
Category : Javascript 02-06-2020 by Luigi Nori
How to Take Your Small Ecommerce Business to the Next Level
Running an ecommerce business can be both exciting and financially rewarding. However, as you increase your customer base, it might seem difficult to successfully scale your operations. If your site is growing in popularity, or you want to attract more customers to your online venture, read the below top tips on…
Category : Web marketing 25-01-2022 by Janeth Kent
Onion Search Engine: How to browse the Deep Web without Tor
The general recommendation does not change: Anyone interested in entering the Deep Web will get a more complete and secure experience by downloading a copy of the Tor Browser, and modifying various browsing habits. However, the desire to "take a look" is always present, and for those cases there is…
Category : Security 25-05-2020 by Janeth Kent
How to turn your smartphone into a webcam for your pc
With the propagation of Covid-19 we all had to adapt to a new quarantine situation at home, and since the human being needs to communicate constantly, we used the internet channel to make group calls, be it between friends or business meetings. This has led to a rapid expansion of online…
Category : Multimedia 17-05-2020 by Luigi Nori
How to Build a Successful E-Commerce Store
Launching an e-commerce store is a popular route for entrepreneurs to take. The thought of opening a physical retail outlet isn’t very appealing in 2020, but here’s what you need to know to build your own e-commerce store. Pick a Business Name and Buy Your Domain It is worth putting some serious…
Category : Web marketing 12-05-2020 by Silvia Mazzetta
Introduction to BEM (Block Element Modifier)
Problems with naming CSS classes I think I might not be the only one with this experience: after finally grasping all the important concepts regarding CSS I wanted to start giving what I thought would be beautiful yet simple style to my HTML code. But suddenly I ended up with class…
Category : Css 23-05-2020 by Iveta Karailievova
How to Change Your DNS Server (And Why You Should)
It's so easy to connect to the internet that you don't think much about how it actually works. You've likely heard about things like IP address, ethernet, DNS servers, or similar terms. They often come up when you try to diagnose internet problems on your home network. Though, this time…
Category : Networking 09-05-2020 by Luigi Nori
Seo: How Search Behavior Has Changed During COVID-19 Pandemic
Google positioning is experiencing a before and after with the coronavirus crisis. The way we search in Google has changed; The way Google the search engine gives us the results has changed ; The tools that webmasters have at their disposal have changed. Google claims that it has never registered as many searches for…
Category : Seo & sem 08-05-2020 by Silvia Mazzetta
How to get into the Deep Web: a guide to access TOR, ZeroNet, Freenet and I2P
We would like to present you with a guide that will allow you to enter the main darknets that make up the Dark Web, colloquially known as the Deep Web, although this last term has another meaning. The hidden Internet or Dark Web is a portion of the network in…
Category : Security 07-05-2020 by Janeth Kent
What is Google My Business and how does it help my local business?
Google My Business is increasingly present in the digital marketing strategies of companies, and this Google tool provides us with various options to better position our business in the search engine. Through the creation of a business file we can work on the SEO of our brand. Google My Business mixes the…
Category : Web marketing 02-05-2020 by Luigi Nori
Online Marketing Strategies for your Ecommerce
The impetus and desire we have to launch our online store can be counterproductive if we have not defined a pre-launch strategy. If we are determined to launch our ecommerce without having stopped to think if we are doing it right, there is a good chance that we will fail. That…
Category : Web marketing 20-04-2023 by Silvia Mazzetta
How To Effectively Learn Coding For Website Development
Building a website can be pretty expensive, especially if you decide to engage a professional. That’s why sometimes, it’s best to take matters into your own hands and develop your own website. You might start by visiting those quick online sites that let you design your web page and learn…
Category : Programming 21-04-2020 by Luigi Nori
Protect yourself: know which apps have access to your location, microphone and camera
When you install an application on your smartphone, you decide what permissions you give it, but it's not always clear. We tell you how to know if those permissions are too much... Smartphones have become the target of choice for hackers and criminals who want to make money or extort money…
Category : News and events 20-04-2020 by Silvia Mazzetta
The best websites of the Tor Deep Web and Dark Web Network
We already talked about Deep Web more than a year ago, explaining that to open Deep Web (or rather Dark Web) sites you need total and undetectable user anonymity and access to the "onion" network. The Dark Web is much smaller than the Deep Web and is composed mainly of sites…
Category : Security 03-11-2022 by Janeth Kent
The exciting story of JavaScript (in brief)
Javascript is a client-side programming language that has changed the Internet as we know it today. The term "client side" means that it runs on our web browser without the need for a web hosting. Along with html and css it is one of the 3 pillars of web design. It is…
Category : Javascript 13-04-2020 by Silvia Mazzetta
How to check if the GPS works
Have you tried to share your location with some friends but couldn't because the GPS on your smartphone looks dead? Don't jump to conclusions - your phone may not be having hardware problems. In fact, GPS malfunctions are often caused by temporary problems due to poor signal reception or poor…
Category : News and events 10-04-2020 by Silvia Mazzetta
5 ways to improve your user experience
As a brand, UX is incredibly important when it comes to keeping your customers happy and on your site. Afterall, the longer they are on your site, the more likely they are to spend, and the more likely you are to hit your targets and KPI’s. Also, the better the…
Category : Ui/ux design 09-04-2020 by Silvia Mazzetta
5 Fool-Proof Ideas For Location-Based Apps
Like it or not, geolocation is a part of our everyday lives. In fact, you’ll find the technology pre-installed on 90% of the apps currently living on your smartphone. Location-based apps are here to stay, which makes them a lucrative option for mobile app developers looking to take advantage of…
Category : Software 01-04-2020 by Luigi Nori
Amazing Javascript Game Source Codes for Free
In this article we will share the code to make simple games with Javascript programming language. The games code can later be your reference material for making other simple games. Before you continue do you already know what is javascript programming ?, if you don't know yet, please read the brief…
Category : Javascript 19-07-2022 by Luigi Nori
How to find everything you need on the Deep Web and the Dark Web
How to find everything you need on the Deep Web and the Dark Web Best links, sites, markets what you can find on the Deep Web The Deep Web is also known as the Deep Internet is a sort of layer of content that is not indexed by the search engines…
Category : Security 10-05-2021 by Silvia Mazzetta
Best Free Image Optimization Tools for Image Compression
Our monitors are getting better and better and, of course, we want to make them profitable by enjoying images with an increasing resolution when we browse. The problem is that this only increases the weight of the web pages, slowing down their load (and thus degrading the user's experience). Something…
Category : Software 27-03-2020 by Janeth Kent
How to Improve Your Website to Attract Local Customers
If you run a small business, make no mistake: local search is imperative for your success. You might have lofty dreams of attracting the world to your website, but it’s those local visitors who will make the difference. This is because 80% of people will try and find local information with…
Category : Web marketing 18-03-2020 by
Linux for Dummies: Introduction
If you have thought about migrating from Windows to a Unix operating system, or Linux specifically there are things you should know. The goal is to give essential information (and not) to take the first steps in the world of the "penguin". What is Linux? With the word Linux we commonly refer…
Category : Operating systems 21-08-2020 by Alessio Mungelli
How to see the websites visited during the incognito mode and delete them
One of the features of any browser's incognito mode is that it does not store visited web pages in history. However, there is a method for displaying the last sites you accessed with your browser, regardless of whether or not you set it to incognito mode. They will all appear in…
Category : Security 21-02-2020 by Silvia Mazzetta
How the Java Swing is Worthy in Designing the Photo Editing App
When social media is reigning over the world, no wonder photography is one of the crucial factors in today’s field of personal or professional recognition. Tons of applications. Still, the demand is far from ending. Online queries are swarming with searches for better graphics toolkit. The better the framework, the…
Category : Java 03-04-2023 by Janeth Kent
Tips to Maximize Your ROI with Google AdWords
The marketing method you use is not important. What you want is the best possible ROI. The money spent should come back to you tenfold. Well, that might be a bit of an exaggeration, but you get the idea. If you were to try pay per click and Google AdWords in…
Category : Seo & sem 22-01-2020 by Silvia Mazzetta