Darknet: the unknown places
People who surf the Dark Web are not necessarily looking for something illegal. Most people want to protect their privacy. And according to a recent study, 93 percent only use websites that are freely accessible.
It is almost impossible not to leave traces on the Internet and therefore reveal a lot of personal information. The "normal" Internet, often commercial, lives off the trade in this data, which most users have known for about 20 years.
Users deliver their data to major Internet platforms when they want to know how to get from A to B faster, for example, with the help of a navigation system or a map provider. Users are often asked for this data politely and in small print. Sometimes this data is secretly taken out of their pockets and often the data that was thought to be safe ends up in the public eye because it has been poorly protected.
Cybercrime
If these data fall into the wrong hands, the consequences can be fatal. Data leaks make it increasingly easy for cyber-crooks to commit serious crimes by manipulating identities, credit card information or other sensitive information.
Not only criminals: also states have a great interest in the enormous amount of data on the Internet. Because if these pieces of the puzzle are put together correctly, the result is a very accurate profile of each person, the dream of all surveillance states.
More than a place for criminals
Whoever surfs the "normal internet", does not know much about the Dark Web, at most he assumes that drugs, weapons and child pornography are traded there. Of course, the Dark Web is also an ideal place for criminals, but it is not as sinister as its reputation. After all, there are good reasons to move around in these anonymous networks, unrecognized by commercial data seekers or invasive regimes.
For people in autocratic states, these data represent a great danger. If a government forbids access to free information, reading the BBC or DW news can be as suspicious as exchanging opinions on social platforms.
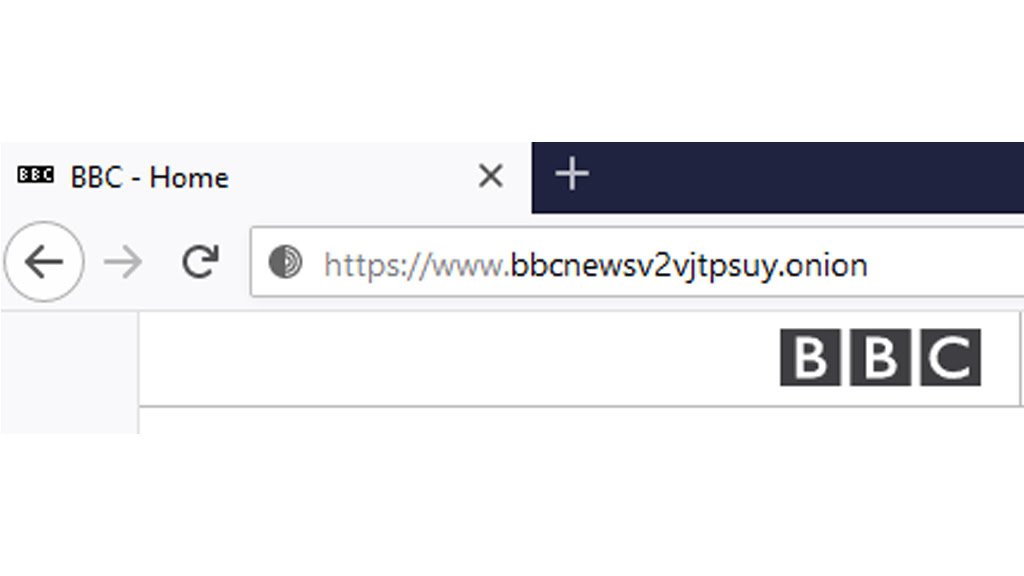
Web pages with the ".onion" domain are not accessible outside the Tor network
In many parts of the world, civil rights activists, journalists and social minorities in particular must fear the worst reprisals if their fingerprints become visible on the internet, either due to state surveillance or internet platforms that do not adequately protect user data.
Multiple protection through the onion system
Whoever wants to enter the darkness without state control, needs special access software. This door opener is for most the Tor browser, an abbreviation for "The Onion Router". This reference to the onion comes from the three layers surrounding the actual data, making it anonymous. Tor is a huge computer network that transmits data back and forth until the sender and receiver can no longer be traced.
Because access to the Tor network can be blocked relatively easily, as has been the case for years in countries such as China, Iran, and most recently Belarus, Tor offers access through so-called Bridges. These are computers that provide the first jump to the Tor network and have IP addresses that change frequently. This means that entry to the Tor network can no longer be blocked. To make sure that it is not noticed that it is a Tor communication later, Internet packets are additionally camouflaged.
With its websites on the Tor network, DW also offers content for countries with limited freedom of expression.
To access the "normal" Deutsche Welle page (dw.com), you exit the Tor network at an Exit Node. By monitoring both input nodes and output nodes, you can bypass Tor anonymization. If an Onion-type tool is used instead, the bypass through an exit node is not necessary and the website can be visited safely within the Tor network. Also, Onion service web pages load even faster with the Tor browser because the additional path through the exit node is no longer necessary.
Who uses Tor and for what
Researchers at Virginia Tech and Skidmore Universities in New York State wanted to know who was really using the Tor network and what content was being accessed. To do this, they used their own server, an Entry Guard, which is one of three layers of Tor anonymized onions. None of the three servers know who the sender and recipient are, each having only partial knowledge.
The entry node doesn't record much about the user, but it can guess whether the user is accessing a web address outside the Tor network that would be accessible with a normal browser, without using the Tor browser. Or if the user is accessing a so-called Onion-Service, that is, websites that end with the domain ".onion" and are not accessible outside the Tor network.
The results of the U.S. study were surprising: 93 percent of all websites accessed through Tor were open-access websites that did not actually require Tor. So obviously, users are more concerned about protecting their privacy. Only 6.7% used Tor to visit sites with the ".onion" domain.
If you want to try your hand at the darknet, try reading the Best Websites of The Tor Deep Web and Dark Web Network, but beware! Here we suggest a guide to safely enter the darkweb.
Important sources of information in authoritative countries
The US researchers' study assumes that most ".onion" sites offer illegal content, because with such a domain the website provider can also remain anonymous. So whoever uses addresses ending in ".onion", is looking for drugs, weapons or child pornography, the American researchers assume.
However, serious content providers on the Dark Web do not want to accept this extremely simplified interpretation. Information providers like the BBC, the New York Times, or BuzzFeed officially operate websites on the Tor network. And Deutsche Welle is also accessible with the Tor browser at dwnewsvdyyiamwnp.onion.
Information providers like the BBC, the New York Times or Deutsche Welle offer with their Onion websites a special service for people from countries with restrictions on press freedom and state surveillance. Their visits remain absolutely anonymous and leave no trace. In addition, the Tor system does not allow you to block websites.
Failure of the objective?
According to the U.S. study, Onion service websites are consulted much less frequently (4.8 percent) in countries with very restricted freedom of information than in free democracies (7.8 percent). However, the study does not explicitly consider the use of Bridges, which are used by people in countries with limited freedom of information. In these countries, VPN access is often used in conjunction with Tor, which was also not considered in the study.
So the US study did not shed much light on the Dark Web. At least it shows that more than 90 percent use the Tor network to protect their privacy when they visit "normal" websites.
In the really dark corners of the Dark Web, illegal activities continue to take place. However, if the entire Tor network were shut down at once, civil rights activists, opposition activists, and journalists from non-Free Countries would also be deprived of all safe communication and independent information.

