390 results for: system
How to include a JavaScript file in another JavaScript file
Category : Javascript 25-09-2024 by Janeth Kent
The best and most amazing Alexa Hacks you should know about
Category : Operating systems 30-06-2023 by Janeth Kent
Google Play Games on PC: Transforming Your Gaming Experience
Category : Videogames 06-06-2023 by Janeth Kent
Top best AI Image Generators: unlocking creativity with Artificial Intelligence
Category : Technology 26-07-2025 by Janeth Kent
The Payment Request API: Revolutionizing Online Payments (Part 2)
Category : Javascript 08-06-2023 by Silvia Mazzetta
Android Hidden Codes: unveiling custom dialer codes and their functionality
Category : Mobile 02-06-2023 by Janeth Kent
Let's create a Color Picker from scratch with HTML5 Canvas, Javascript and CSS3
Category : Web design 01-06-2023 by Janeth Kent
Mastering array sorting in JavaScript: a guide to the sort() function
Category : Javascript 29-05-2023 by Janeth Kent
Is AI sexist? A gender perspective in Robotics and Artificial Intelligence
Category : News and events 22-05-2023 by Silvia Mazzetta
Should Your Social Media Strategy Always Be Ready for a Crisis?
Category : Social networks 01-06-2023 by Janeth Kent
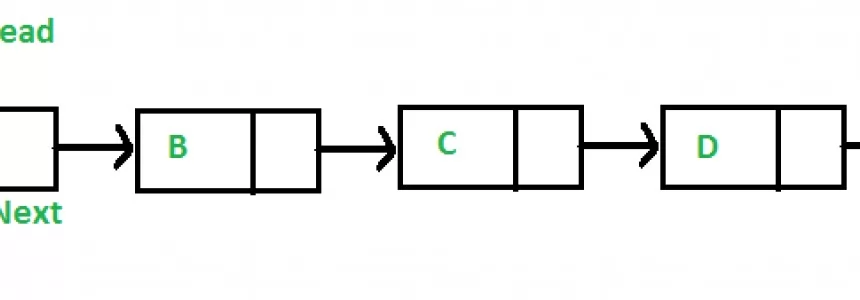
Infinite scrolling with native JavaScript using the Fetch API
Category : Javascript 05-11-2024 by Janeth Kent
The history of video games: from entertainment to virtual reality
Category : Videogames 28-11-2022 by Janeth Kent
Does Google's artificial intelligence have feelings?
Category : Technology 04-08-2022 by Janeth Kent
Why E-Commerce Businesses Should be Using Cloud Computing
Category : Web marketing 01-06-2021 by Silvia Mazzetta
The ultimate cybersecurity checklist for programmers
Category : Security 02-06-2023 by Silvia Mazzetta
Advanced Android tutorial: discover all your phone's secrets
Category : Mobile 06-05-2021 by Janeth Kent
How to set up your Android phone: learn how to get your new phone up and running
Category : Mobile 28-04-2021 by Janeth Kent
How to improve customer experience through speech recognition
Category : Technology 27-04-2021 by Janeth Kent
Parental controls on Android: how to make mobiles and tablets child-friendly
Category : Security 26-04-2021 by Janeth Kent
How To Use Varnish As A Highly Available Load Balancer On Ubuntu 20.04 With SSL
Category : Servers 25-04-2021 by Janeth Kent
Elon Musk To Found Starbase, A City In Texas To House His Companies And Projects
Category : Technology 05-03-2021 by Janeth Kent
Deepfakes Detection – An Emerging Technological Challenge
Category : Technology 27-01-2021 by Iveta Karailievova
Understanding LCP, CLS, FID. All about Core Web Vitals in Google Search Console
Category : Seo & sem 14-01-2021 by
Read comics online: best websites and apps to download and read digital comics
Category : News and events 26-05-2023 by Silvia Mazzetta
How to make the website's dark mode persistent with Local Storage, CSS and JS
Category : Css 22-12-2020 by
Dark Web: the creepy side of the Internet is not as dark as believed
Category : Security 17-05-2023 by Silvia Mazzetta
The BleedingTooth vulnerability and other Bluetooth security risks
Category : Security 10-11-2020 by Iveta Karailievova
The best tricks and features to master your Android Smart TV
Category : Networking 05-11-2020 by Luigi Nori
Why You Should Hire Node.js Developer for Your Backend Development
Category : Javascript 27-10-2020 by Luigi Nori
What's the Difference between Google TV and Android TV?
Category : Software 27-10-2020 by Silvia Mazzetta
3 awesome ways technology is helping us combat the COVID pandemic
Category : Technology 28-10-2020 by Iveta Karailievova
The new features coming to the Google search engine in autumn 2020
Category : Seo & sem 18-10-2020 by Luigi Nori
How to turn an Android device into a retro game console
Category : Software 14-10-2020 by Silvia Mazzetta
A Dev compile and install Windows XP and Server 2003 from filtered source code
Category : Operating systems 08-10-2020 by Luigi Nori
Jennifer in Paradise: story of the first photo ever edited in Photoshop
Category : News and events 25-09-2020 by Silvia Mazzetta
How to securely access the Dark Web in 15 steps. Second part
Category : Security 08-03-2024 by Janeth Kent
How to securely access the Dark Web in 15 steps. First part
Category : Security 08-03-2024 by Silvia Mazzetta