89 results for: communication
Transitioning from a Home Office to a Virtual Office
Category : Web marketing 08-03-2024 by Janeth Kent
The Importance of Maintaining a Crisis-Ready Social Media Strategy: A Closer Look
Category : Social networks 01-06-2023 by Janeth Kent
Should Your Social Media Strategy Always Be Ready for a Crisis?
Category : Social networks 01-06-2023 by Janeth Kent
Does Google's artificial intelligence have feelings?
Category : Technology 04-08-2022 by Janeth Kent
The man who married a hologram: fact or fiction? The story of Akihiko Kondo
Category : News and events 19-07-2022 by Janeth Kent
Dark Web: the creepy side of the Internet is not as dark as believed
Category : Security 17-05-2023 by Silvia Mazzetta
Cross cultural challenges in web design, an overview
Category : Web design 21-12-2020 by Maria Antonietta Marino
The BleedingTooth vulnerability and other Bluetooth security risks
Category : Security 10-11-2020 by Iveta Karailievova
How to securely access the Dark Web in 15 steps. Second part
Category : Security 08-03-2024 by Janeth Kent
Suggestions to Improve the Efficiency of a Small Business
Category : Web marketing 26-07-2025 by Janeth Kent
How are businesses using artificial intelligence?
Category : News and events 21-06-2023 by Silvia Mazzetta
How to integrate native images lazy loading in your web projects
Category : Programming 03-04-2023 by Luigi Nori
7 Killer Strategies to Increase Your Sales Funnel Conversion Rates
Category : Web marketing 23-07-2020 by Janeth Kent
Awesome JavaScript Games and Js Software to create Games
Category : Javascript 30-06-2020 by Janeth Kent
Why do you vote the way you do in the age of misinformation and fake news?
Category : News and events 11-06-2020 by Silvia Mazzetta
Step by Step Guide to Successful Social Media Marketing
Category : Web marketing 16-05-2023 by Silvia Mazzetta
The best websites of the Tor Deep Web and Dark Web Network
Category : Security 03-11-2022 by Janeth Kent
Best ways to start a video conference without registration
Category : Multimedia 21-04-2020 by Silvia Mazzetta
How They Can Hack You While Navigating: Protecting Your Digital Security
Category : Security 23-06-2023 by Silvia Mazzetta
How Technology has Improved the Way We Do Business
Category : Web marketing 20-06-2019 by Janeth Kent
RCS: Everything you need to know about the successor to the SMS
Category : Mobile 18-06-2019 by Janeth Kent
10 Collaborative Coding Tools for Remote Pair Programming
Category : Development 02-03-2020 by Janeth Kent
Pulsetuit, the new platform for sentiment analysis in real time
Category : Software 19-02-2020 by Janeth Kent
What You Need to Know When Sending a Press Release to Newswire
Category : News and events 25-02-2019 by Janeth Kent
The Importance of Other People to the Success of Your Website
Category : Web marketing 27-02-2018 by Janeth Kent
How Our Relationship with the Internet has Changed in the Last 20 Years
Category : News and events 29-04-2021 by Janeth Kent
Ten Laws of Successful Social Media and Content Marketing
Category : Social networks 13-06-2020 by Silvia Mazzetta
An Introduction to Email Segmentation: Boosting Engagement and Personalization
Category : Web marketing 23-06-2023 by Janeth Kent
Ubuntu servers security: 25 security tools to armor your system
Category : Servers 14-09-2016 by Janeth Kent
8 Social Tools to interact with Customers and improve CX
Category : Social networks 22-07-2016 by Janeth Kent
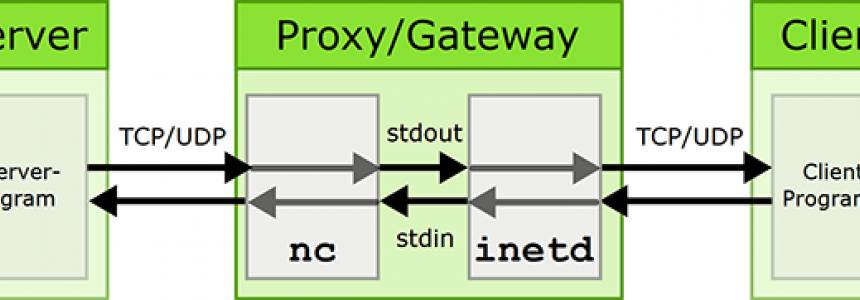
How to create a Twitter proxy for mobile development
Category : Programming 06-12-2013 by Janeth Kent
50 Top Tools for Social Media Monitoring, Analytics, and Management
Category : Social networks 15-05-2013 by Janeth Kent
Transform A Simple Website in Vibrant Ecommerce Portal
Category : Web design 04-05-2020 by Silvia Mazzetta