69 results for: lists
How to Use ChatGPT to automatically create Spotify playlists
Category : Technology 23-06-2023 by Janeth Kent
Dark Web: the creepy side of the Internet is not as dark as believed
Category : Security 17-05-2023 by Silvia Mazzetta
Python or Swift: Revealing Benefits and Drawbacks of Each Language and Their Differences
Category : Programming 04-03-2021 by
Website Traffic Getting Low? 4 Immediate Action to Take
Category : Web marketing 04-12-2020 by Luigi Nori
The BleedingTooth vulnerability and other Bluetooth security risks
Category : Security 10-11-2020 by Iveta Karailievova
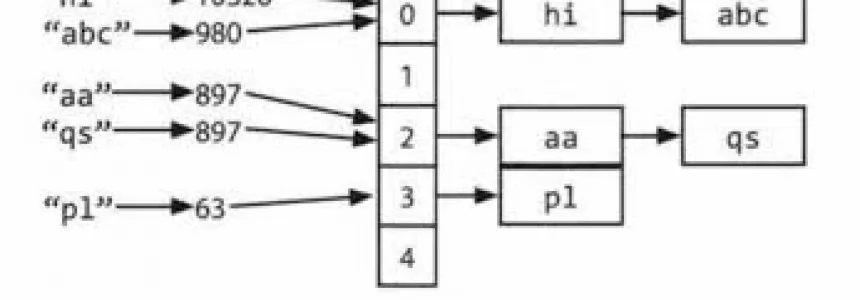
Hashmap: hashing, collisions and first functions
Category : C language 28-06-2020 by Alessio Mungelli
How to securely access the Dark Web in 15 steps. First part
Category : Security 08-03-2024 by Silvia Mazzetta
What cybersecurity professionals have learned from the lockdown experience
Category : Security 26-08-2020 by Silvia Mazzetta
The best websites of the Tor Deep Web and Dark Web Network
Category : Security 03-11-2022 by Janeth Kent
How the Java Swing is Worthy in Designing the Photo Editing App
Category : Java 03-04-2023 by Janeth Kent
Implement Internationalization in Javascript (a headache for developers)
Category : Javascript 12-07-2019 by Janeth Kent
Progressive Web Apps Directory: The Best Collection of Resources
Category : Javascript 20-06-2019 by Janeth Kent
How to Create your own custom Linux system, step by step
Category : Operating systems 14-06-2019 by Janeth Kent
What You Need to Know When Sending a Press Release to Newswire
Category : News and events 25-02-2019 by Janeth Kent
Superior React-Native Courses for Mobile Application Developers
Category : Programming 24-11-2019 by Janeth Kent
Four of the Biggest Reasons Your Emails are Sent to Spam
Category : Web marketing 14-08-2018 by Janeth Kent
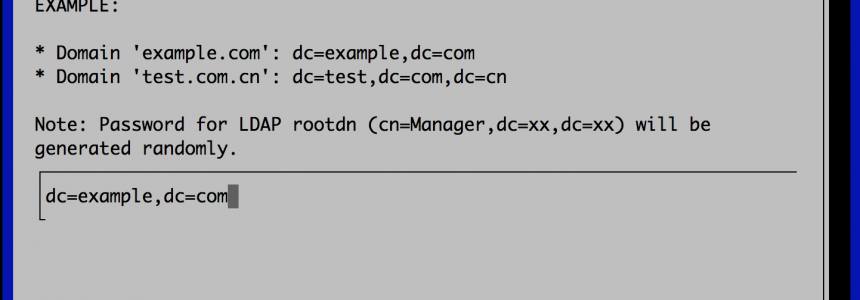
How to Set up a Fully Functional Mail Server on Ubuntu 16.04 with iRedMail
Category : Networking 30-03-2023 by Janeth Kent
Increase the Number of Backlinks to Your Site the Right Way
Category : Seo & sem 18-03-2020 by Janeth Kent
Ubuntu servers security: 25 security tools to armor your system
Category : Servers 14-09-2016 by Janeth Kent
PHP7: Guide and References to all the changes between version 5.x and 7 of PHP
Category : Php 27-12-2015 by Janeth Kent
How Companies can Drive Engagement with Blogs: 50 tips
Category : Web marketing 21-08-2013 by Janeth Kent
12 Must Read Tips and Tricks For Web-Design And Web-Dev Addicts
Category : Web design 16-07-2013 by Janeth Kent
50 tools to reinvigorate your content marketing efforts
Category : Web marketing 03-07-2013 by Janeth Kent
20 Open Source Scripts Applications for Web Developers
Category : Programming 11-08-2016 by Janeth Kent
25 Useful HTML5 Tools For Web Designers & Developers
Category : Web design 29-05-2013 by Janeth Kent
50 Top Tools for Social Media Monitoring, Analytics, and Management
Category : Social networks 15-05-2013 by Janeth Kent
Super Stealthy Backdoor Spreads To Hit Hundreds Of Thousands Of Web Users
Category : Security 09-05-2013 by Janeth Kent
Enhance Your Google+ Experience With These Fantastic Tools
Category : Social networks 08-05-2013 by Janeth Kent
Penguin 2.0 Forewarning: The Google Perspective on Links
Category : Web marketing 11-04-2013 by Janeth Kent
20 Best Wireframing Tools for Web Designers and Developers
Category : Web design 11-04-2013 by Janeth Kent
Transform A Simple Website in Vibrant Ecommerce Portal
Category : Web design 04-05-2020 by Silvia Mazzetta
A list of Great PHP libraries and classes you should know
Category : Programming 26-03-2021 by Janeth Kent