43 results for: monitoring
The Importance of Maintaining a Crisis-Ready Social Media Strategy: A Closer Look
Category : Social networks 01-06-2023 by Janeth Kent
Cumulative Layout Shift, what is and How to optimize CLS
Category : Seo & sem 14-01-2021 by Luigi Nori
Dark Web: the creepy side of the Internet is not as dark as believed
Category : Security 17-05-2023 by Silvia Mazzetta
What cybersecurity professionals have learned from the lockdown experience
Category : Security 26-08-2020 by Silvia Mazzetta
Web shells as a security thread for web applications
Category : Security 04-05-2020 by Iveta Karailievova
Coronavirus: Citizen Science projects to help research from home
Category : News and events 02-04-2020 by Silvia Mazzetta
Unlock Hidden SmartPhone Features with these Secret Codes
Category : Security 26-07-2025 by Janeth Kent
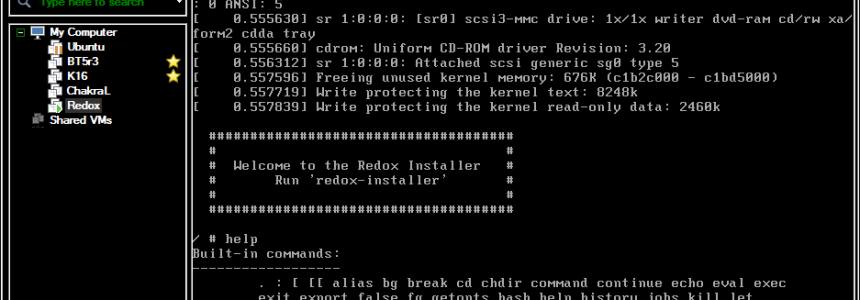
80 Linux Network Monitor Software & Tools for Managing & Monitoring Unix/Linux Systems
Category : Security 23-10-2018 by Janeth Kent
Useful Terminal Commands Every Web Developer Should Know About
Category : Operating systems 22-06-2018 by Janeth Kent
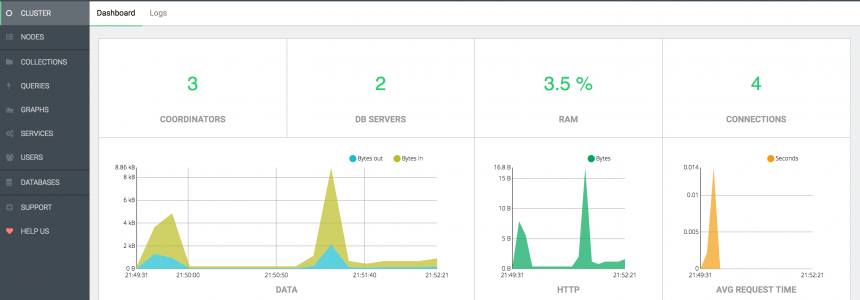
ArangoDB, install and configure the popular Database in ubuntu 16.04
Category : Databases 14-11-2017 by Janeth Kent
Top 8 Free Online Social Media Marketing Tools For Startups
Category : Web marketing 08-11-2022 by Janeth Kent
Ubuntu servers security: 25 security tools to armor your system
Category : Servers 14-09-2016 by Janeth Kent
8 Social Tools to interact with Customers and improve CX
Category : Social networks 22-07-2016 by Janeth Kent
Display Linux TCP / UDP Network and Socket Information with the 'ss' command
Category : Networking 23-05-2020 by Janeth Kent
Guide: Install Free SSL Certificate On Your Website with Let's Encrypt
Category : Networking 09-05-2020 by Janeth Kent
20 Open Source Scripts Applications for Web Developers
Category : Programming 11-08-2016 by Janeth Kent
50 Top Tools for Social Media Monitoring, Analytics, and Management
Category : Social networks 15-05-2013 by Janeth Kent
Open Source Cloud Is Failing To Gain Traction: Survey
Category : Web marketing 09-05-2013 by Janeth Kent
WARNING: New Malware Threat in Twitter's Topics
Category : News and events 23-04-2013 by Janeth Kent
The Best tools that may come in handy in your online life
Category : Software 01-05-2020 by Janeth Kent