52 results for: protection
The ultimate cybersecurity checklist for programmers
Category : Security 02-06-2023 by Silvia Mazzetta
We Will Soon Be Able To Use Bitcoins With Traditional Visa and Mastercard Cards
Category : Technology 22-03-2021 by Janeth Kent
Elon Musk To Found Starbase, A City In Texas To House His Companies And Projects
Category : Technology 05-03-2021 by Janeth Kent
htaccess Rules to Help Protect from SQL Injections and XSS
Category : Security 01-03-2021 by Janeth Kent
Dark Web: the creepy side of the Internet is not as dark as believed
Category : Security 17-05-2023 by Silvia Mazzetta
The best tricks and features to master your Android Smart TV
Category : Networking 05-11-2020 by Luigi Nori
Why You Should Hire Node.js Developer for Your Backend Development
Category : Javascript 27-10-2020 by Luigi Nori
How to securely access the Dark Web in 15 steps. Second part
Category : Security 08-03-2024 by Janeth Kent
How to securely access the Dark Web in 15 steps. First part
Category : Security 08-03-2024 by Silvia Mazzetta
How to install a Linux partition on a Windows 10 PC
Category : Operating systems 06-09-2020 by Luigi Nori
What cybersecurity professionals have learned from the lockdown experience
Category : Security 26-08-2020 by Silvia Mazzetta
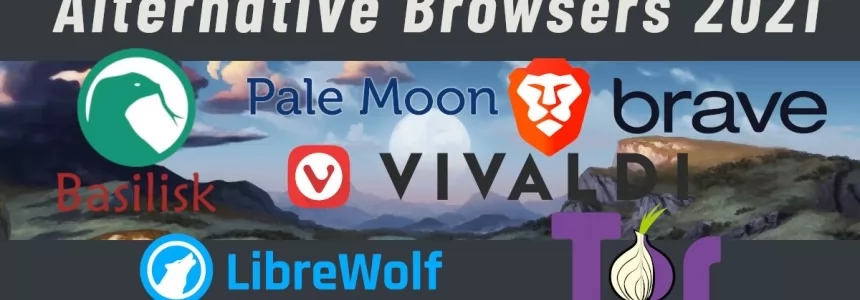
How to configure Tor to browse the deep web safely
Category : Security 12-08-2020 by Silvia Mazzetta
Web shells as a security thread for web applications
Category : Security 04-05-2020 by Iveta Karailievova
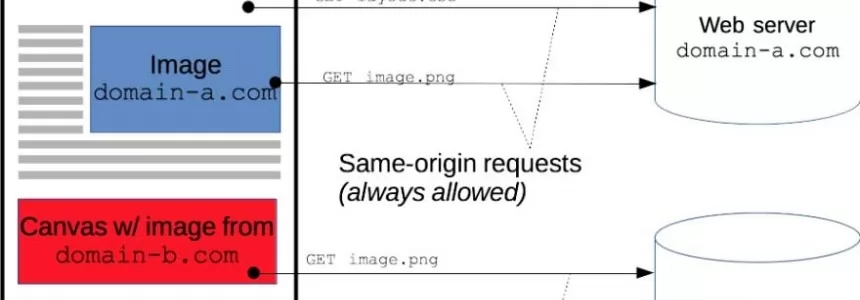
Cross-Origin Resource Sharing (CORS) and examples of XSS and CSRF
Category : Javascript 30-01-2020 by Luigi Nori
How the Java Swing is Worthy in Designing the Photo Editing App
Category : Java 03-04-2023 by Janeth Kent
How They Can Hack You While Navigating: Protecting Your Digital Security
Category : Security 23-06-2023 by Silvia Mazzetta
RCS: Everything you need to know about the successor to the SMS
Category : Mobile 18-06-2019 by Janeth Kent
Vuejs and GDPR : how to be compliant with new EU regulations
Category : Javascript 21-09-2018 by Janeth Kent
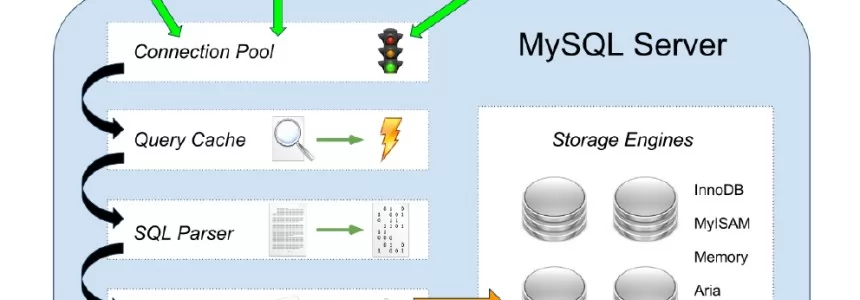
How to Configure the Mod_Security Core Ruleset in Ubuntu
Category : Servers 04-03-2017 by Janeth Kent
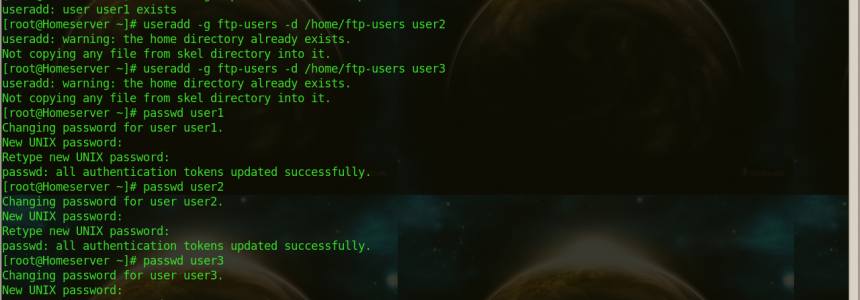
Ubuntu servers security: 25 security tools to armor your system
Category : Servers 14-09-2016 by Janeth Kent
Speed up your site and protect it against DDOS attacks with CloudFlare
Category : Networking 23-07-2014 by Luigi Nori
Ubuntu UFW Firewall - Uncomplicated Firewall for Ubuntu
Category : Networking 27-05-2013 by Janeth Kent
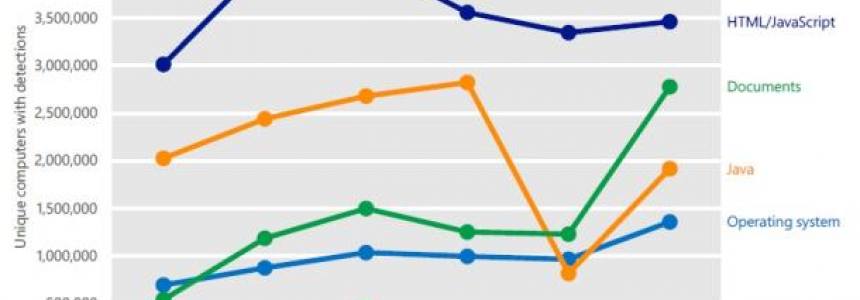
Mobile Malware Targets Android Phones: new Kaspersky Lab report
Category : Security 23-05-2013 by Janeth Kent
A list of Great PHP libraries and classes you should know
Category : Programming 26-03-2021 by Janeth Kent