People tend to confuse the terms Deep Web and Dark Web, and while they are related, they are not exactly the same. The Deep Web is essentially the entire Internet that's out of reach of traditional search engines, and it can encompass everyday things like emails from a Gmail account, direct messages from Facebook, and even content marked private in a service as popular as YouTube.
On the other hand, the Dark Web is basically the dark side of the Deep Web (as its name suggests), encompassing drug trafficking, weapons and online accounts stolen or coming from hackers that sometimes have not been detected by their victims. It is logical that all these markets do everything possible to avoid being exposed, because if detected their portals would end up closed in most cases for engaging in illegal activities.
However, not all of the Dark Web is the preserve of criminals. There are also other websites that operate legally or at least do not initially carry out any illegal activity. The five websites mentioned below can be visited with Tor Browser or using some VPN with Tor support.
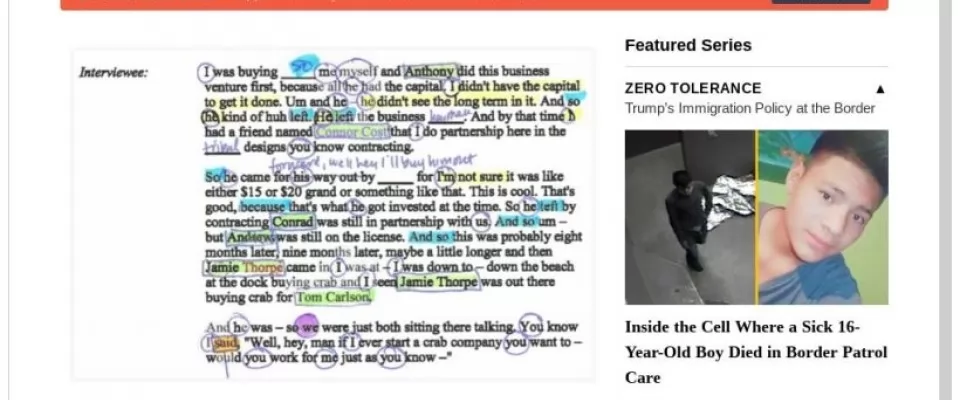
ProPublica version for Dark Web
ProPublica is one of the first news websites to have decided to be officially displayed on the Dark Web, having made the decision in 2016. It is a non-profit news organization that aims to expose abuses of power and betrayals of public trust by government, business and other institutions, using investigative journalism.
Far from being a little-known or niche medium, ProPublica has won five Pulitzer Prizes, the last one this 2019, which was awarded to Hannah Dreier for coverage of Los Angeles gangs.
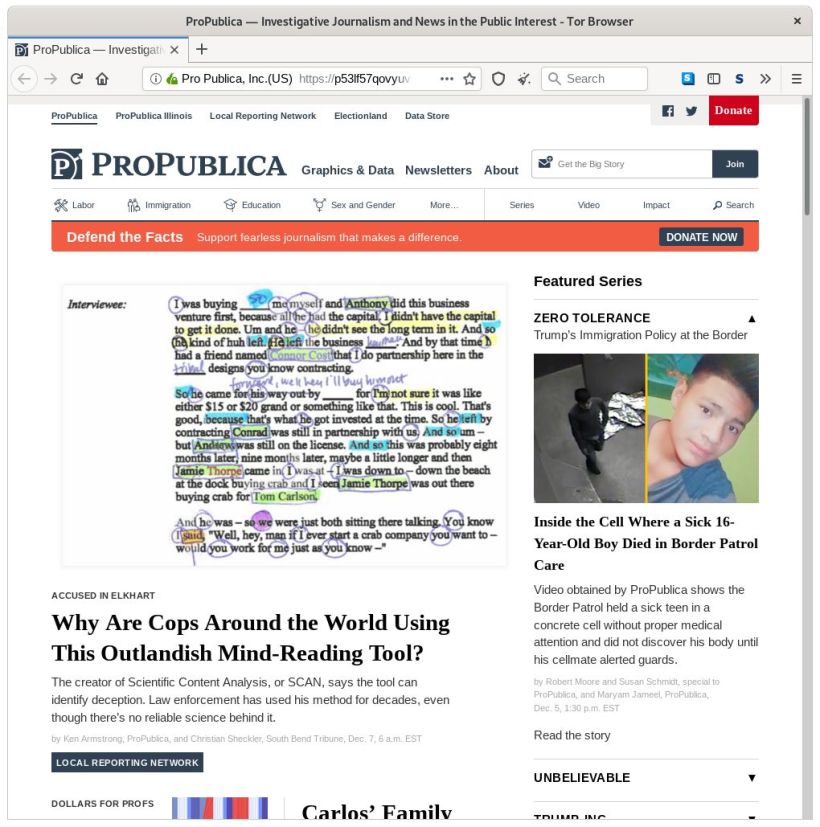
Mail2Tor
Email is one of the least secure means of communicating. To know this you only have to use the same Google Account (Gmail) for both the mail and the search engine. The user will be able to see that the results of searches may end up being altered according to the correspondence they have received, and even discover that the search engine asks them if they want to publish their opinion on a product they have recently bought.
This is where Mail2Tor comes in as an alternative provider, as it allows you to send and receive emails anonymously both from the webmail and using an email, encrypting all the messages and preventing companies from registering the IP used by the user.
OnionDomain
Obviously, if you want to host your own website with a .onion domain, you will have to get a domain name.
OnionDomain allows you to get a non-sensitive domain for free, but you have to pay if you want to have a personalized domain. Due to their special consideration, .onion domains cannot be obtained through registrars that act publicly and openly, but it is necessary to resort to some specialized service.
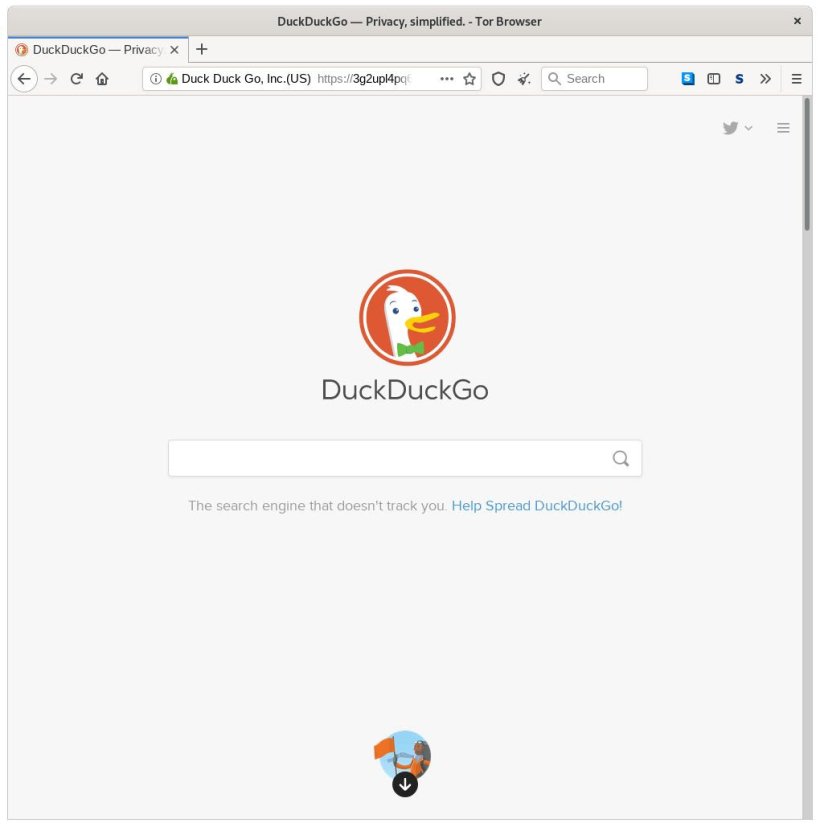
DuckDuckGo version for Dark Web
The well-known alternative search engine DuckDuckGo, strongly focused on privacy, also has a version of its site on the Dark Web.
For those who don't know it, DuckDuckGo is Google's best-known competitor in its segment. While the Mountain View giant's search engine is very powerful and may even be more effective at performing certain technical searches, it has the drawback of carrying out a crawl that some privacy advocates find excessive.
For its part, DuckDuckGo does not track user activity (history, location, etc.), but it does display advertising based on the term that has been entered in the search bar (the website has to live from something).
And what does the Dark Web version of DuckDuckGo offer? Well, something as simple as an extra layer of privacy and anonymization.
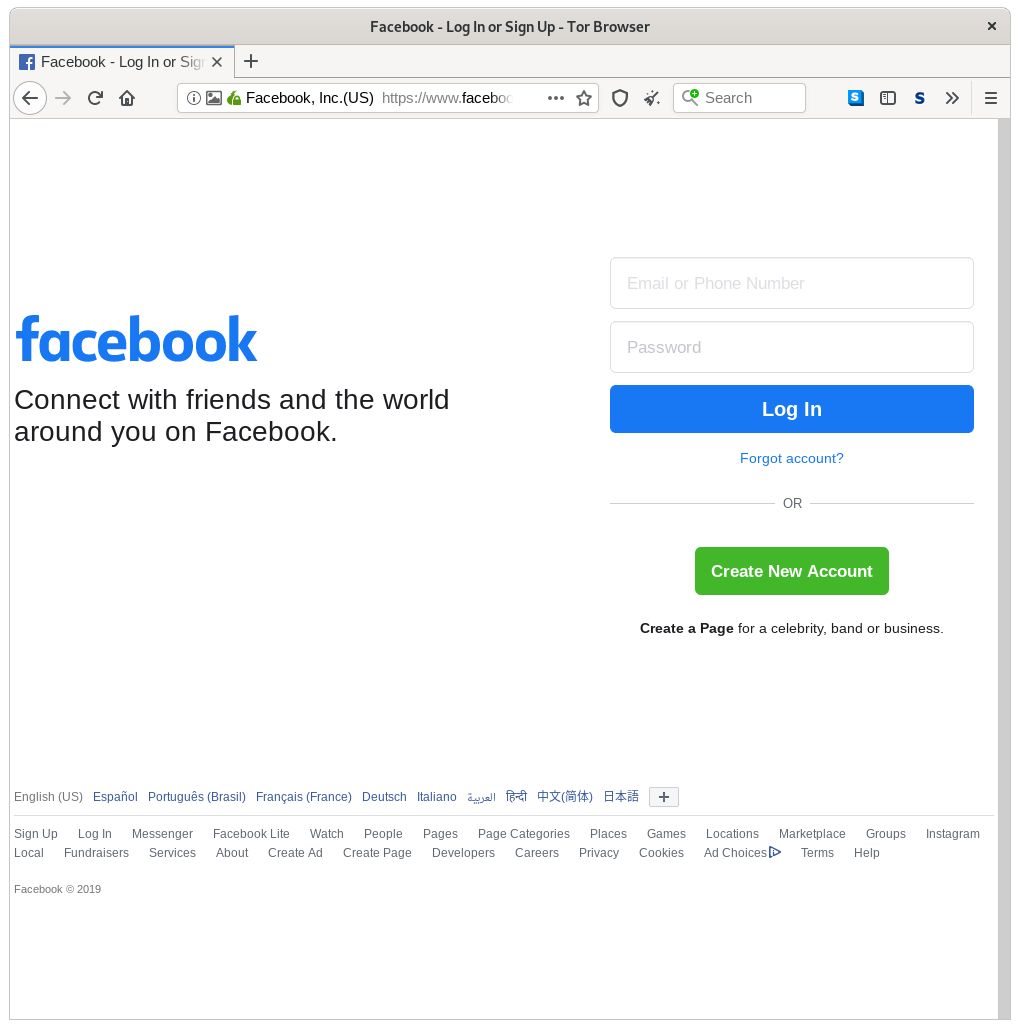
Facebook version for Dark Web
Surprised? For many it may be a paradox that Facebook, one of the most criticized privacy companies in the world, has a mirror on the Dark Web with .onion domain.
Using the Facebook mirror on the Dark Web has two benefits: it allows you to create and use an anonymous account and use the services of the popular social network without being trapped by its questionable privacy mechanisms.
Although this may sound like a contradiction in terms of Facebook's trajectory, the existence of this version of the social network could have the purpose of making it available in countries where it is censored, such as China.
Conclusion
The Dark Web is a world that covers practically everything, and in addition to illegal activities or questionable legality, is also used by some as a means to avoid censorship, especially in some countries where fundamental rights are violated, which often results in the inability to access media that are not controlled or authorized by the government.