Setting up your own mail server from scratch on Linux is complex and tedious, until you meet iRedMail. This tutorial is going to show you how you can easily and quickly set up a full-fledged mail server on Ubuntu 16.04 with iRedMail under 30 minutes.
What is iRedMail?
iRedMail is a shell script that automatically install and configure all necessary mail server components on your Linux/BSD server and thus eliminates manual installation and configuration. Supported OS are as follows:
- RHEL/CentOS
- Debian/Ubuntu
- FreeBSD/OpenBSD
Open-source software used in iRedMail:
- Postfix
- Dovecot
- Apache, Nginx
- OpenLDAP, ldapd
- MySQL/MariaDB, PostgreSQL
- Amavised-new
- SpamAssassin
- ClamAV
- Roundcube webmail
- SOGo Groupware
- Fail2ban
- Awstats
- iRedAPD
iRedMail features:
- All components are open-source.
- TLS is enabled by default. SMTP/IMAP over TLS, HTTPS webmail
- Create as many virtual mailboxes as you want in a web-based admin panel.
- Stores mail accounts in OpenLDAP, MySQL/MariaDB, or PostgreSQL.
It is recommended that you follow the instructions below on a clean install of Ubuntu 16.04 system that has at least 2GB of RAM, as after the installation your server will use more than 1GB of RAM. Don’t run this iRedMail server alongside your website or blog on the same machine, unless you are confident that you can restore the virtual host file for your website or blog, because the installation process will break your existing virtual hosts.
Before the Installation
First, make sure your server IP isn’t listed in any email blacklist. You can go to mxtoolbox.com and dnsbl.info to check your server IP address. If it’s in a blacklist, you can delete your VPS instance in Linode and create a new one. As Linode uses an hourly billing model, you won’t be charged by month, but by how many hours you used, which makes it convenient to delete a VPS instance.
Once you have a server with good IP reputation, SSH into your Ubuntu 16.04 server and update all software.
sudo apt update;sudo apt upgrade
Then set a fully qualified domain name (FQDN) for your server with the following command.
sudo hostnamectl set-hostname mail.your-domain.com
We also need to update /etc/hosts file.
sudo nano /etc/hosts
Edit it like below:
127.0.0.1 mail.your-domain.com localhost
Save and close the file. To see the changes, re-login and use the following command to see your hostname.
hostname -f
Don’t forget to set MX record and A record for your domain name. The MX record should point to your mail server’s FQDN,
Record Type Name Value
MX @ mail.your-domain.com
The A record points to your mail server’s IP address.
Record Type Name Value
A mail IP-address-of-mail-server
If your server uses IPv6 address, be sure to add AAAA record.
Setting up a Mail Server on Ubuntu 16.04 with iRedMail
Next, download the iRedMail Bash installer with wget. At the time of writing, the latest version of iRedMail is 0.9.7, released on July 1, 2017. Please go to iRedMail download page (http://www.iredmail.org/download.html) to check out the latest version.
wget https://bitbucket.org/zhb/iredmail/downloads/iRedMail-0.9.7.tar.bz2
Extract the tarball.
tar xvf iRedMail-0.9.7.tar.bz2
Then cd into the newly created directory.
cd iRedMail-0.9.7/
Add executable permission to the iRedMail.sh script.
chmod +x iRedMail.sh
Next, run the Bash script with sudo privilege.
sudo bash iRedMail.sh
The ncurse-based setup wizard will appear. Select Yes.
The next screen will ask you to select the mail storage path. You can use the default one /var/vmail.
Next, choose your preferred web server: Apache or Nginx. You need to use up and down arrow and press the spacebar to select.
Then select the storage backend. Choose one that you are familiar with. This tutorial chose MariaDB.
If you selected MariaDB or MySQL, then you will need to set the MySQL root password.
Please note that if you selected MariaDB, then you don’t need password to log into MariaDB shell. Instead of running the normal command:
mysql -u root -p
you can run the following command to login, with sudo and without providing MariaDB root password. This is because MariaDB uses unix_socket authentication plugin, which allows users to use OS credentials to connect to MariaDB. But you still need to set root password in iRedMail setup wizard.
sudo mysql -u root
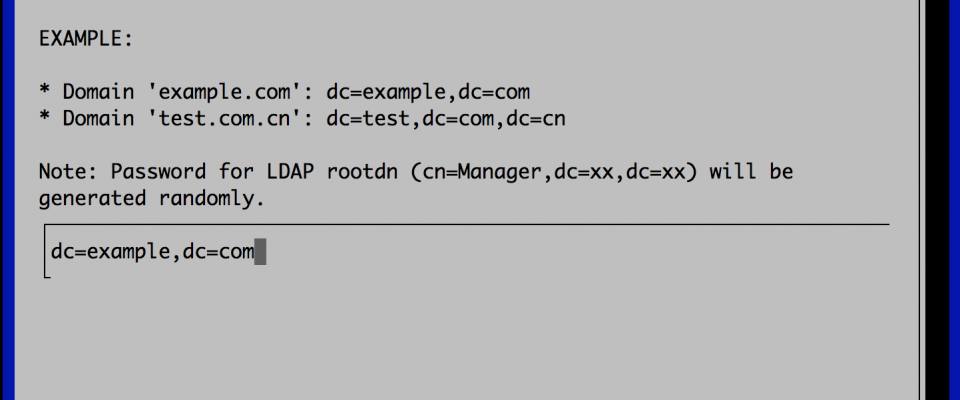
Next, enter your first mail domain. You can add multiple mail domains later in the web-based admin panel. This tutorial assumes that you want an email account like [email protected], in that case, you need to enter your-domain.com here, without sub-domain.
Next, set a password for the mail domain administrator.
Choose optional components.
Now you can review your configurations. Type Y to begin the installation of all mail server components.
At the end of installation, choose y to use firewall rules provided by iRedMail and restart firewall.
Now iRedMail installation is complete. You will be notified the URL of webmail, SOGo groupware and web admin panel and the login credentials. The iRedMail.tips file contains important information about your iRedMail server.
******************************************************************** * URLs of installed web applications: * * - Roundcube webmail: httpS://mail.your-domain.com/mail/ * - SOGo groupware: httpS://mail.your-domain.com/SOGo/ * * - Web admin panel (iRedAdmin): httpS://mail.your-domain.com/iredadmin/ * * You can login to above links with below credential: * * - Username: [email protected] * - Password: ********* * * ******************************************************************** * Congratulations, mail server setup completed successfully. Please * read below file for more information: * * - /home/gourd/iRedMail-0.9.5-1/iRedMail.tips * * And it's sent to your mail account [email protected]. * ********************* WARNING ************************************** * * Please reboot your system to enable all mail services. * ********************************************************************
Reboot your Ubuntu 16.04 server.
sudo shutdown -r now
Once your server is back online, you can visit the web admin panel.
https://mail.your-domain.com/iredadmin/
Because it’s using a self-signed TLS certificate, so you need to add security exception. Login with the postmaster mail account.
In the Add tab, you can add multiple domains or mail users.
After you create a user, you can visit the Roundcube webmail address and login with the new mail user account.
https://mail.your-domain.com/mail/
And test email sending and receiving. Please note that you may need to wait for a few minutes to receive emails because greylisting is enabled by default. You can change password and create filter in RoundCube.
Installing Let’s Encrypt TLS Certificate
Since the mail server is using a self-signed TLS certificate, both desktop mail client users and webmail client users will see a warning. To fix this, we can obtain and install a free Let’s Encrypt TLS cert.
Obtaining the Certificate
First, install Let’s Encrypt (certbot) client on Ubuntu 16.04.
sudo apt install software-properties-common sudo add-apt-repository ppa:certbot/certbot sudo apt update sudo apt install certbot
The Apache and Nginx configuration directories are heavily modified by iRedMail, so here I recommend using the webroot plugin, instead of using apache or nginx plugin, to obtain certificate. Run the following command. Replace red text with your actual data.
sudo certbot certonly --webroot --agree-tos --email your-email-address -d mail.your-domain.com -w /var/www/html/
You will see the following text indicating that you have successfully obtained a TLS certificate. Your certificate and chain have been saved at /etc/letsencrypt/live/mail.your-domain.com/ directory.
Installing the Certificate
After obtaining a TLS certificate, let’s configure web server to use it.
Apache
If you use Apache web server, then edit the default virtual host file.
sudo nano /etc/apache2/sites-available/000-default.conf
Add the following 3 lines above </VirtualHost>.
RewriteEngine on
RewriteCond %{SERVER_NAME} =mail.your-domain.com
RewriteRule ^ https://%{SERVER_NAME}%{REQUEST_URI} [END,QSA,R=permanent]
The above 3 directives will redirect HTTP connection to HTTPS. The rewrite module needs to be enabled for them to work, which is achieved by executing the following command.
sudo a2enmod rewrite
Then edit the https version of the default virtual host.
sudo nano /etc/apache2/sites-available/default-ssl.conf
Find the following 2 lines.
SSLCertificateFile /etc/ssl/certs/iRedMail.crt SSLCertificateKeyFile /etc/ssl/private/iRedMail.key
We need to replace the self-signed certificate with Let’s Encrypt issued certificate. So the above two lines need to be changed to the following.
SSLCertificateFile /etc/letsencrypt/live/mail.your-domain.com/fullchain.pem SSLCertificateKeyFile /etc/letsencrypt/live/mail.your-domain.com/privkey.pem
Save and close the file. Then reload Apache web server.
sudo systemctl reload apache2
Now if you visit iRedMail admin panel or Roundcube webmail again, you shall see a green lock in the browser address bar.
Nginx
If you use Nginx, then edit the SSL template file.
sudo nano /etc/nginx/templates/ssl.tmpl
Find the following 2 lines.
ssl_certificate /etc/ssl/certs/iRedMail.crt; ssl_certificate_key /etc/ssl/private/iRedMail.key;
Replace them with:
ssl_certificate /etc/letsencrypt/live/mail.your-domain.com/fullchain.pem; ssl_certificate_key /etc/letsencrypt/live/mail.your-domain.com/privkey.pem;
Save and close the file. Then test nginx configuration and reload.
sudo nginx -t sudo systemctl reload nginx
Visit iRedMail admin panel or Roundcube webmail again, you shall see a green lock in the browser address bar.
Configuring Postfix and Dovecot
We also need to configure Postfix and Dovecot to use the Let’s Encrypt issued certificate so that desktop mail client won’t display security warning. Edit the main configuration file of Postfix.
sudo nano /etc/postfix/main.cf
Find the following 3 lines. (line 95, 96, 97).
smtpd_tls_key_file = /etc/ssl/private/iRedMail.key smtpd_tls_cert_file = /etc/ssl/certs/iRedMail.crt smtpd_tls_CAfile = /etc/ssl/certs/iRedMail.crt
Replace them with:
smtpd_tls_key_file = /etc/letsencrypt/live/mail.your-domain.com/privkey.pem smtpd_tls_cert_file = /etc/letsencrypt/live/mail.your-domain.com/cert.pem smtpd_tls_CAfile = /etc/letsencrypt/live/mail.your-domain.com/chain.pem
Save and close the file. Then reload Postfix.
sudo postfix reload
Next, edit the main configuration file of Dovecot.
sudo nano /etc/dovecot/dovecot.conf
Fine the following 2 lines. (line 47, 48)
ssl_cert = </etc/ssl/certs/iRedMail.crt ssl_key = </etc/ssl/private/iRedMail.key
Replace them with:
ssl_cert = </etc/letsencrypt/live/mail.your-domain.com/fullchain.pem ssl_key = </etc/letsencrypt/live/mail.your-domain.com/privkey.pem
Save and close the file. Then reload dovecot.
sudo dovecot reload
From now on, desktop mail users won’t see security warnings.
Auto Renew TLS Certificate
To auto renew certificate, simply open root user’s crontab file.
sudo crontab -e
Then add the following line at the bottom of the file.
@daily letsencrypt renew --quiet && /usr/sbin/postfix reload && /usr/sbin/dovecot reload && systemctl reload apache2
If you use Nginx, then replace systemctl reload apache2 with systemctl reload nginx. Reloading is necessary to make these programs pick up the new certificate and private key.
Creating PTR, SPF, DKIM Records
To prevent your emails from being flagged as spam, you should set PTR, SPF and DKIM records.
PTR record
A pointer record, or PTR record, maps an IP address to a FQDN. It’s the counterpart to the A record and is used for reverse DNS lookup. Reverse resolution of A record with PTR record can help with blocking spammers. Many MTAs accept email only if the server is really responsible for a certain domain.
To check the PTR record for an IP address:
dig -x <IP> +short
or
host <IP>
Because you get IP address from your hosting provider, not from your domain registrar, so you must set PTR record for your IP in the control panel of your hosting provider and its value should be your mail server’s hostname: mail.your-domain.com. If your server uses IPv6 address, be sure to add a PTR record for your IPv6 address.
SPF Record
SPF (Sender Policy Framework) record specifies which hosts or IP address are allowed to send emails on behalf of a domain. You should allow only your own email server or your ISP’s server to send emails for your domain.
In your DNS management interface, create a new TXT record like below.
TXT @ v=spf1 mx ~all
Explanation:
- TXT indicates this is a TXT record.
- Enter @ in the name field.
- v=spf1 indicates this is a SPF record and the SPF record version is SPF1.
- mx means all hosts listed in the MX records are allowed to send emails for your domain and all other hosts are disallowed.
- ~all indicates that emails from your domain should only come from hosts specified in the SPF record. Emails that are from other hosts will be flagged as forged.
Note that some DNS managers require you to wrap the SPF record with quotes like below.
TXT @ "v=spf1 mx ~all"
To check if your SPF record is propagated to the public Internet, you can use the dig utility on your Linux machine like below:
dig your-domain.com txt
The txt option tells dig that we only want to query TXT records.
DKIM Record
DKIM (DomainKeys Identified Mail) use a private key to add a signature to emails sent from your domain. Receiving SMTP servers verify the signature using the pubic key published in your DNS manager.
The iRedMail script automatically configured DKIM for your server. The only thing left to do is creating DKIM record in DNS manager. Open the iRedMail.tips file under iRedMail-0.9.7 directory.
sudo nano iRedMail.tips
Scroll down to DNS record for DKIM support section.
Then in your DNS manager, create a TXT record, enter dkim._domainkey in the name field. Copy everything in the parentheses and paste into the value field. Delete all double quotes and white spaces.
After creating PTR, SPF, DKIM record, go to https://www.mail-tester.com. You will see a unique email address. Send an email from your domain to this address and then check your score.
Mail-tester.com can only show you a sender score. There’s a better service called GlockApps that allow you to check if your email is landed in the recipient’s inbox or spam folder, or rejected outright. It supports many popular email providers like Gmail, Outlook, Hotmail, YahooMail, iCloud mail, etc.
Adding Multiple Mail Domains
If you want to add another mail domain, then you need to
- add a new mail domain and user in iRedMail admin panel.
- create MX, A and SPF record for the new mail domain.
- tell amavisd to sign email messages for the new domain.
Add MX record like below.
Record Type Name Value
MX @ mail.new-domain.com
The A record points to your mail server’s IP address.
Record Type Name Value
A mail IP-address-of-mail-server
If your servers uses IPv6 address, be sure to add AAAA record.
Then create SPF record to allow the MX host to send email for the new mail domain.
Record Type Name Value TXT @ v=spf1 mx ~all
Next, you need to tell amavisd to sign every email message for the new mail domain. You can use the existing private key to sign the new domain. Edit /etc/amavis/conf.d/50-user file.
sudo nano /etc/amavis/conf.d/50-user
Find the following lines in the file.
@dkim_signature_options_bysender_maps = ( {
...
"your-domain.com" => { d => "your-domain.com", a => 'rsa-sha256', ttl => 10*24*3600 },
...
});
Add the following line to tell amavisd to sign with the same private key. Note that new_domain.com is your second mail domain. your-domain.com is the first mail domain.
"new_domain.com" => { d => "your-domain.com", a => 'rsa-sha256', ttl => 10*24*3600 },
So the configurations will be changed to the following.
@dkim_signature_options_bysender_maps = ( {
...
"your-domain.com" => { d => "your-domain.com", a => 'rsa-sha256', ttl => 10*24*3600 },
"new_domain.com" => { d => "your-domain.com", a => 'rsa-sha256', ttl => 10*24*3600 },
...
});
Save and close the file. Then restart amavisd.
sudo systemctl restart amavis
Since we are using the the same private key for signing, there’s no need to add DKIM record for the new domain. Reverse DNS check is used to check if the sender’s IP address match the HELO hostname (the hostname you set at the beginning of this tutorial), so you don’t need to add another PTR record when adding a new mail domain. Now you can use the new domain to send and receive emails. Don’t forget to test your score at https://www.mail-tester.com.
Using Separate Domain for RoundCube
It makes sense to let users of the first domain use mail.domain1.com and users of the second domain use mail.domain2.com when using RoundCube webmail. All you need to do is create another virtual host in Apache or another server block in Nginx. However, as I said before, the Apache/Nginx directory structure is heavily modified by iRedmail, which makes the process a little complicated.
Don’t worry, just follow the instructions below if you use Nginx. (I currently don’t use Apache on my mail server, so I can’t show the exact step for Apache users, but the idea applies to Apache. You just need to change a few things to make it work.)
Change working directory to /etc/nginx/.
cd /etc/nginx/
Create a blank server block file for the second domain in /etc/nginx/sites-enabled/ directory.
sudo touch sites-enabled/mail.domain2.com.conf
Copy the default HTTP site configurations to the file.
cat sites-conf.d/default/* | sudo tee -a sites-enabled/mail.domain2.com.conf
Copy the default SSL site configurations to the file.
cat sites-conf.d/default-ssl/* | sudo tee -a sites-enabled/mail.domain2.com.conf
Edit the file.
sudo nano sites-enabled/mail.domain2.com.conf
Make the following changes.
- Wrap all configurations with
server {...}block. - Change the vaule of
server_nametomail.domain2.com. - Comment out
include /etc/nginx/templates/redirect_to_https.tmpl;. - Comment out
include /etc/nginx/templates/ssl.tmpl;. - Comment out duplicate lines.
Now the file looks like below.
Save and close the file. Then test Nginx configurations.
sudo nginx -t
If the test is successful, reload Nginx.
sudo systemctl reload nginx
Install Certbot Nginx plugin.
sudo apt install python-certbot-nginx
Obtain and install a free Let’s Encrypt certificate by using the Nginx plugin.
sudo certbot --nginx --agree-tos --redirect --staple-ocsp -d mail.domain2.com --email your-email-address
Now you should be able to use separate domains to access RoundCube webmail.
That’s it! I hope this tutorial helped you set up a mail server with iRedMail on Ubuntu 16.04.