results for: tech
How to Start a Web Design Agency in 2022
If the last two years have shown us anything, it’s that a good online presence is paramount to success in the modern world of business. Once they have a robust web-based reputation in place, companies have the capacity to disrupt their sectors in an engaging, intuitive, and ultimately profitable fashion.…
Category : Web marketing 25-01-2022 by Janeth Kent
Secret iPhone codes to unlock hidden features
We love that our devices have hidden features. It's fun to learn something new about the technology we use every day, to discover those little features that aren't advertised by the manufacturer. And unless you spend a lot of time playing around in the Phone app, you probably don't know, until…
Category : Security 22-10-2021 by Silvia Mazzetta
JavaScript Arrow functions: What they are and how to use them
In this article we are going to see what they are and how to use JavaScript Arrow Functions, a new feature introduced with the ES6 standard (ECMAScript 6). What are Arrow Functions Arrow Functions are a new syntax for defining anonymous functions in JavaScript in a more concise way. Being an abbreviated…
Category : Javascript 30-08-2021 by Janeth Kent
What is a Full Stack Developer?
The demand for the Full Stack Developer is growing exponentially in recent years. Disruptive technology companies and startups are increasingly requesting this type of multipurpose profile that knows multiple programming languages and can assume all kinds of functions within the company. Throughout this article we will tell you what a full stack…
Category : News and events 06-08-2021 by Janeth Kent
Why E-Commerce Businesses Should be Using Cloud Computing
Cloud computing is the on-demand delivery of computer system resources via the internet. The resources offered in a cloud computing solution include data storage applications, servers, databases, software, and networking tools. Cloud computing seems like it’s been created specifically for businesses like e-commerce stores, as it offers increased flexibility and…
Category : Web marketing 01-06-2021 by Silvia Mazzetta
Are you being floCed by Google?
No panic! Don't be alarmed, because it may sound worse than it is. But since Google doesn't seem to have any intention of communicating it properly, it's up to the rest of us to do so. We're talking about the new secure tracking system with which the Internet giant wants…
Category : News and events 21-05-2021 by Janeth Kent
The ultimate cybersecurity checklist for programmers
In today's digital age, cybersecurity has become an essential concern for programmers. With cyber threats on the rise, it is crucial for programmers to adopt robust security practices to protect their code, data, and systems from malicious attacks. To assist programmers in this endeavor, we have compiled the ultimate cybersecurity…
Category : Security 02-06-2023 by Silvia Mazzetta
Top JavaScript libraries and frameworks part 1
JavaScript libraries and frameworks make it easy to develop websites and applications with a wide variety of features and functionality, all with dynamic, flexible and engaging features. According to a 2020 StackOverflow survey, JavaScript remains the most widely used programming language (for the eighth year), with 67.7% of respondents using it. Its…
Category : Javascript 06-05-2021 by Janeth Kent
Network attacks and how to avoid them
Nowadays it is impossible to list all the different types of attacks that can be carried out on a network, as in the world of security this varies continuously. We bring you the most common ones according to the network attack databases, so that we can keep up to date…
Category : Security 03-05-2021 by Silvia Mazzetta
How to improve customer experience through speech recognition
Voice of the Customer (VoC) is essential to a successful customer experience (CX) programme. However, VoC data is often disparate, making it difficult to use. Service organisations looking to make more informed decisions about customer experience (CX) investments and improvements should implement a consistent voice of the user (VoC) strategy,…
Category : Technology 27-04-2021 by Janeth Kent
Top tools for UX design and research
This article is a compilation of the "ux tools" I have tested in recent years. I've separated the tools by categories, although I recommend you to take a look at all of them, you might find some you didn't know. - Conceptualisation and project management tools - UX testing and research tools - Analytics…
Category : Ui/ux design 23-04-2021 by Silvia Mazzetta
6 Best Alternative Privacy Focused Browsers in 2021
In today's article we take a look at free private browsers which are relevant in 2021. We will compare their advantages and disadvantages, specs, etc. Let's get into it. What are alternative browsers? Alternative browsers are mostly trying to increase browser security, by various methods, such as browser hardening, sandboxing, encryption forcing, etc. When…
Category : Software 22-04-2021 by
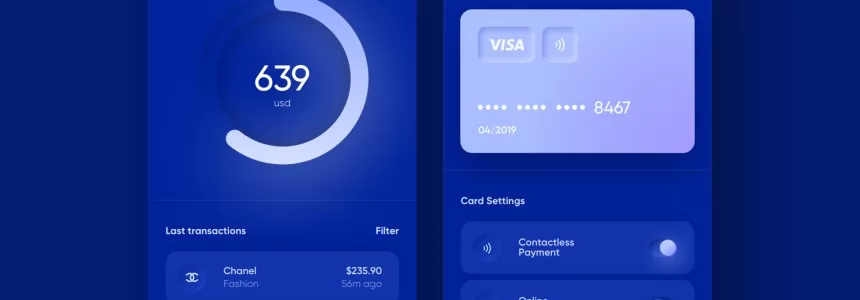
We Will Soon Be Able To Use Bitcoins With Traditional Visa and Mastercard Cards
Bitcoin is breaking records, surpassing $60,000 and being presented in the media as a revolution in many ways. Industry giants cannot continue to ignore the trend, and now VISA has spoken out. The CEO of VISA commented in Fortune's Leadership Next podcast that they are working to make it possible to…
Category : Technology 22-03-2021 by Janeth Kent
SEO: How to choose the best Anchor Text
Anchor Text are the words used to insert a link within a piece of content. This text can be anything from "click here" to the name of a brand or even a series of keywords or phrases. When choosing the best anchor text, always put the user experience first. Since the launch…
Category : Seo & sem 15-03-2021 by Janeth Kent
Bootstrap 5 beta2. What offers?
Since the release of the Bootstrap 4 is three years, in this article we will present what is new in the world’s most popular framework for building responsive, mobile-first sites. If you want to know what are the significant changes that come with the next version 5 which is in…
Category : Css 05-04-2021 by
Top Graphic Design e-Books & How to Get them on Your iDevice
Ma-no.org may include links to commercial websites. A commercial website is defined as a business site designed to generate income through the provision of services and products. Where links to commercial sites are included on ma-no.org, this does not indicate or imply any affiliation or endorsement between that commercial entity…
Category : Ui/ux design 03-03-2021 by Luigi Nori
Top 7 Potential Tools for Automation Testing
Today's digital economy has significantly changed how organizations deliver products and services. Many organizations are gravitating towards smart methodologies and automated tools to spark customer interest in their products and increase revenue to ensure quality and speedy deliveries. These testing tools help organizations to determine the expected and actual product delivery…
Category : Web marketing 12-02-2021 by Janeth Kent
Interesting and Helpful Google Search Features You’ll Want to Start Using
Google – THE search engine for many internet users. It has been with us since its launch back in 1998 and thanks to its simplicity of use and genius algorithms, it grew so popular, that most of us cannot imagine our day-to-day life without it. Many petty arguments between friends…
Category : Software 31-01-2021 by Iveta Karailievova
Graphic design and its impact on Web Development
In today's article we will explain the concept of graphic design, its fundamentals and what it brings into web development. Graphic design is applied to everything visual, believe or not, it can aid in selling a product or idea, it's applied company identity as logos, colors, typography of the company…
Category : Web design 05-04-2021 by
Deepfakes Detection – An Emerging Technological Challenge
It is highly probable that while browsing the Internet, everyone of us has at some point stumbled upon a deepfake video. Deepfakes usually depict well-known people doing really improbable things – like the queen of England dancing on her table or Ron Swanson from Parks and Recreations starring as every…
Category : Technology 27-01-2021 by Iveta Karailievova
Top Whatsapp alternatives in 2021
From the communication platform WhatsApp leaves more and more users for different reasons. If you're one of them, there are a lot of possibilities on how to replace it with something better. We will show you what are the 5 free alternatives to WhatsApp to have a text or audio-video conversation…
Category : Software 26-01-2021 by
Understanding LCP, CLS, FID. All about Core Web Vitals in Google Search Console
A few months ago we talked about certain Google metrics that were displayed in Search Console. The reason for writing another post on this topic is that Google has changed this again, giving priority to other metrics. Interestingly, we thought in that previous study that the FCP and FID were not…
Category : Seo & sem 14-01-2021 by Laura Celis Ballesta
7 Astonishing New Uses of Machine Learning
Recently a strange video published on YouTube caused a controversy – it was a funny take on Queen Elizabeth’s traditional Christmas message created by Channel 4, a British public-service television broadcaster. They used AI to produce a fake video of the Queen making it look very realistic and if the message itself…
Category : Technology 31-12-2020 by Iveta Karailievova
What is DNS Blockchain and how to use it
To be able to navigate the Internet, to enter a website and have it show us all the content we want and search for, certain functions and characteristics are necessary. One of these key points is the DNS. It is what translates domain names into IP addresses, which prevents us…
Category : Security 28-12-2020 by Janeth Kent
How to use Parallax.js effect on your website
Today, we're going to write about the parallax effect, similar to parallax scrolling, and how to implement it to improve your landing page. In webdev, they say mobile first - well, this engine will react to the movement of a smart device, offsetting layers depending on their depth within a…
Category : Javascript 26-12-2020 by
What is Django and what is it used for
When we talk about Django, we refer to that framework that is used for any totally free and open source web application which is written in Python. Basically, it's a group of elements that will help you create web pages much more easily and quickly. At the moment you are going…
Category : Programming 26-12-2020 by Janeth Kent
Django vs. Laravel: Market Share Comparison
There are two leading frameworks in the web development segment: Django and Laravel. In this article, we prepared a Django and Laravel comparison focusing on their market share so that you can figure out which framework is better for your project. Selecting the appropriate framework is crucial for coping with…
Category : Programming 23-12-2020 by Janeth Kent
SEO: How to find and remove artificial links
At Ma-no we are aware of the importance of a good linkbuilding strategy in order to achieve success with a website. Links are key to placing a website among the top positions in Google search results, and therefore increasing the number of visits and conversions. But in today's post we are not…
Category : Seo & sem 23-12-2020 by Silvia Mazzetta
How to get paid in Bitcoin: CoinBase, CoinGate
After explaining how bitcoins work and how to pay using this cryptocurrency, we will see how to get paid in bitcoin. Below you will find explained in detail how to do it. Many people find the concept of BitCoin virtual currency confusing. We could simply explain that BitCoin is a peer-to-peer financial…
Category : Technology 23-12-2020 by Silvia Mazzetta
How to make the website's dark mode persistent with Local Storage, CSS and JS
Recently we wrote about how to do a switchable alternative color mode or theme, a very useful and popular feature to websites. Today’s article is going to be about how to store a user’s settings on your website, specifically, how to save dark mode settings and restore it when a…
Category : Css 22-12-2020 by
Dark Web: the creepy side of the Internet is not as dark as believed
People who surf the Dark Web are not necessarily looking for something illegal. Most people want to protect their privacy. And according to a recent study, 93 percent only use websites that are freely accessible. It is almost impossible not to leave traces on the Internet and therefore reveal a lot…
Category : Security 17-05-2023 by Silvia Mazzetta
Cross cultural challenges in web design, an overview
The user experience design of a product essentially lies between the intentions of the product and the characteristics of your user. - David Kadavy - The task of building a culturally appropriate website for a new market can be challenging: in this article we are going to talk about the impact of national…
Category : Web design 21-12-2020 by Maria Antonietta Marino
Some Neat Ways to Improve Your Internet Browsing Experience?
Not everyone has the best time when they are surfing the net. There are multiple reasons why an internet browser struggles, but that does not mean the situation is out of your hands. Relying on the internet is inevitable these days. We use it for work, entertainment, and socializing with friends…
Category : News and events 21-12-2020 by Janeth Kent
How to pay in Bitcoin: Hype and Coinbase
Once the wallet is created, let's see how to pay in Bitcoin to buy various products and services. If you have opened a Bitcoin wallet with HYPE, you can send payments using this cryptocurrency very easily. All you need to do is go to the Menu section of the HYPE app, press…
Category : Technology 10-12-2020 by Silvia Mazzetta
How to Use Bitcoin: mining, wallets, payments
You have certainly heard of Bitcoin, the virtual currency that periodically makes people talk about itself because of its innovative and particular nature. In this case, you have probably also wondered how it is possible to get and subsequently spend Bitcoins, and if it is something useful, as well as…
Category : Technology 10-12-2020 by Silvia Mazzetta
Security of Internet providers: can we trust it?
This year has been a time of many changes. Now, more people are connected to the Internet through their home routers for teleworking, shopping, or leisure. This is where the security of Internet operators becomes more important. The question is whether the ISP's security is good enough to be the only…
Category : Security 29-05-2023 by Janeth Kent
Google everywhere: anatomy of a massive giant
The alarm clock is going off. A hand floats over the bedside table groping for the source of the sound: probably a cell phone and maybe one of the more than 2.5 billion Android devices in the world. Alphabet's operating system (Google's matrix) concentrates 74.6% of the market and together with…
Category : Technology 03-12-2020 by Silvia Mazzetta
5 Tips to Bring More Traffic to Your Blog
Publishing a blog on your business website is an effective marketing tool for several reasons. Blog posts are the ideal place to share information about your company, products, services, and showcase your expertise or comment on industry trends. Blog posts also give you a space to express more personality, a sense…
Category : Seo & sem 03-12-2020 by Janeth Kent
Brief History of Biometric Authentication
These days, biometric authentication seems to be part of every little gadget or device we use. You’ve no doubt used it when logging onto your laptop, your tablet, or your cell phone, alongside more ‘old school’ methods like a password or PIN. Governments often use biometric authentication for security access and…
Category : Security 30-11-2020 by Janeth Kent
Making AJAX requests to a REST API using vanilla JavaScript and XHR
Imagine you just build your first static web page and you would like to add some functionality to make it more attractive and generally more usable. Perhaps you would like to entertain your web page visitor with randomly generated cat facts, jokes, or, (preferably not randomly generated) weather forecasts or…
Category : Javascript 25-11-2020 by Iveta Karailievova
A beginner’s guide to software vulnerabilities
What are software vulnerabilities The number of devices connected to the Internet is growing every day. And among those devices we find not only computers and smartphones, but also an ever-rising number of cameras, smoke detectors, motion sensors, smart door locks, and let’s not forget that even plant pots. Many households…
Category : Security 17-11-2020 by Iveta Karailievova
The BleedingTooth vulnerability and other Bluetooth security risks
Have you ever heard of BleedingTooth? And we do not mean the really disturbing looking mushroom which goes by this name and is totally real (we double checked) but one of the lately discovered vulnerabilities in Linux systems. It had hit the tech news recently, when Andy Nguyen, a Google security…
Category : Security 10-11-2020 by Iveta Karailievova
A Java Approach: Selection Structures - Use Cases
Hello everyone and welcome back! Up to now we have been concerned to make as complete an overview as possible of the fundamental concepts we need to approach the use of conditional structures. We have therefore introduced the concept of conditional structures, outlining the various situations that could arise. We…
Category : Java 20-10-2020 by Alessio Mungelli
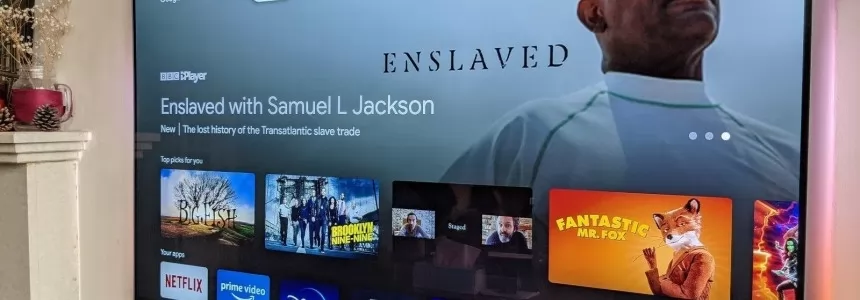
The best tricks and features to master your Android Smart TV
We bring you a collection of the best tricks to squeeze Android TV, the Google operating system designed for televisions. You can find it on smart televisions of some brands, but also on devices that you will connect to the TV. With all of them, you can use different types…
Category : Networking 05-11-2020 by Luigi Nori
A Java approach: boolean variables
The previous time, we talked extensively about Boolean variables, trying to outline the main operations that can be carried out at a practical level. Of all the cases examined, we have not examined the most important and most recurrent one: the case in which the conditions to be examined are more…
Category : Java 18-10-2020 by Alessio Mungelli
Why You Should Hire Node.js Developer for Your Backend Development
When developers are building a new website, they mainly focus on both frontend and backend development. The frontend code helps create the interfaces through which the app interacts with the users while the back-end code interacts with the server to deliver data or content that is displayed to the website…
Category : Javascript 27-10-2020 by Luigi Nori
What's the Difference between Google TV and Android TV?
At the end of September, Google launched the renewal of its classic dongle. The new Google Chromecast didn't arrive alone, but added two very important innovations compared to the devices of previous generations that have been turning normal televisions into smart TVs since 2013. The first of these novelties is the…
Category : Software 27-10-2020 by Silvia Mazzetta
How to watch deleted or private Youtube videos
Today we are going to talk about the technique which you permit to be able to recover videos from Youtube that was deleted, made private or simply blocked by Youtube itself. With this trick you most of the time would do just that. How is this possible we will explain…
Category : Social networks 05-04-2021 by
3 awesome ways technology is helping us combat the COVID pandemic
Times are hard now, that humanity once more stumbled into a terrible pandemic. But in comparison to the poor folks back in 1918 when the Spanish flu was on wreaking havoc, nowadays we have the advantage of cutting edge technology on our side. Here’s a quick list of top three ways…
Category : Technology 28-10-2020 by Iveta Karailievova
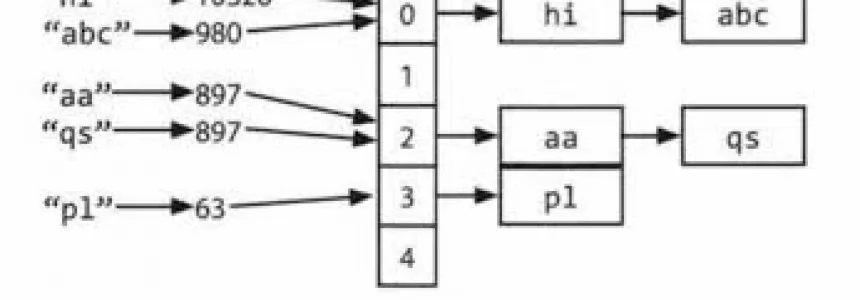
Hashmap: hashing, collisions and first functions
Today we are going to study some concepts closely related to hashmaps. The concepts we are going to see are hashing and collisions. Hashing The idea of hashing with chaining is to create a sort of array of lists, into which the elements are somehow inserted. We need to map the keys to…
Category : C language 28-06-2020 by Alessio Mungelli
How to Unlock Secret Games in Chrome, Edge and Firefox
Your web browser is full of secrets. I usually spend a lot of time studying new features that I can unlock through pages like chrome://flags and about:config in the browser, but sometimes it's also fair and necessary to take a break and play the games that popular browsers hide. Yes, your…
Category : Videogames 07-10-2020 by Silvia Mazzetta
SEO in Google News: How to appear in Google News
Google News is a tool, from Google, that spreads current, reliable and truthful content from different websites or portals dedicated exclusively to news. The sites that appear in Google News have a great opportunity to increase traffic to your website and consequently the opportunity to increase your sales through it. If you…
Category : Seo & sem 26-06-2023 by Luigi Nori
Google Dorks: How to find interesting data and search like hacker
Go the words Google and Hacking together? Well if you thought that we will learn how to use hack Google, you might be wrong. But we can Use Google search engine to find interesting data accidentally exposed to the Internet. Such a simple search bar has the potential to help you also…
Category : Security 03-12-2021 by
Jennifer in Paradise: story of the first photo ever edited in Photoshop
A photograph with more than 30 years of history has become an icon in popular culture, or at least it remains in the memory of those who have ever used Adobe Photoshop, the well-known tool for photo retouching. Behind software like Photoshop there are dozens of stories. One of them…
Category : News and events 25-09-2020 by Silvia Mazzetta
Data Scraping and Data Crawling, what are they for?
Right now we are in an era where big data has become very important. At this very moment, data is being collected from millions of individual users and companies. In this tutorial we will briefly explain big data, as well as talk in detail about web crawling and web scraping…
Category : Web marketing 25-09-2020 by Silvia Mazzetta
How to write our own Privacy Policy
In this article we will talk about Privacy Policy statements, how you can write one and implement it on your page. Why did it pop up? These days when we browse on any new page, or when we visit the site for the first time, most of the time we have to…
Category : Development 13-12-2023 by
How to securely access the Dark Web in 15 steps. Second part
Let's continue with the 2nd part of our article in which we try to give you some advice on how to safely and securely explore the dark web. Let's restart from number 6. 6. Changes the security level in the Tor browser It is also possible to increase the security level of the…
Category : Security 08-03-2024 by Janeth Kent
Suggestions to Improve the Efficiency of a Small Business
If you have a small business, it means that every resource matters. You have less room for error due to a lack of manpower as well as other aspects. So focusing on efficiency is something that ought to be your priority. Of course, inefficient experience is a big hindrance. You may…
Category : Web marketing 25-01-2022 by Janeth Kent
What is a Cryptophone and how it works
The so-called cryptophones, are anti-interception smartphones as they use encryption methods to protect all communication systems. Here are all the details and the truth about these "unassailable" phones. The recent Encrochat affair, recently investigated for illegal activities, has brought to light the so-called cryptophones. They are smartphones - legal in themselves -…
Category : Security 11-09-2020 by Silvia Mazzetta
How to comply with Google's quality guidelines in 2020
Google provides a set of guidelines on what your website's content should look like in order to appear in search results. There are several categories within the Google guidelines: Webmaster Guidelines. General guidelines. Content-specific guidelines. Quality guidelines. In this article we will focus on the Quality guidelines. Quality guidelines, describe techniques whose use is prohibited and which,…
Category : Seo & sem 09-09-2020 by Silvia Mazzetta
How to install a Linux partition on a Windows 10 PC
In spite of a past we could say almost confronted, the approach between Windows and Linux is accelerating more and more, drawing a story closer to love than to hate. So much so that Windows 10 already offers support for Linux natively. Creating a subsystem is no longer penalized. A…
Category : Operating systems 06-09-2020 by Luigi Nori
How are businesses using artificial intelligence?
The term Artificial Intelligence (AI), "the intelligence of the machines", unifies two words that, a priori, could not be associated, since the term intelligence is attributed to the faculty of the mind to learn, to understand, to reason, to take decisions and to form a determined idea of the reality. How…
Category : News and events 21-06-2023 by Silvia Mazzetta
What cybersecurity professionals have learned from the lockdown experience
The COVID-19 pandemic has radically changed the rules of the game for most companies and individuals in a very short time; it has also changed the international computing universe. Sudden changes in people's habits as well as in business operations have altered some of the elements that characterize cyber-risk. And…
Category : Security 26-08-2020 by Silvia Mazzetta
5 Remote Careers You Can Start Online in 2020
In 2020, life has moved indoors. School, shopping, entertainment, and work have all moved online to keep up with the fight against COVID-19. And with it came an enormous demand for remote careers. If you are looking to start a new career that you can excel in without leaving the…
Category : News and events 25-08-2020 by Silvia Mazzetta
The most popular Array Sorting Algorithms In PHP
There are many ways to sort an array in PHP, the easiest being to use the sort() function built into PHP. This sort function is quick but has it's limitations, especially when sorting things like dates as PHP usually guesses which value is higher than the other and can produce…
Category : Php 25-08-2020 by Luigi Nori
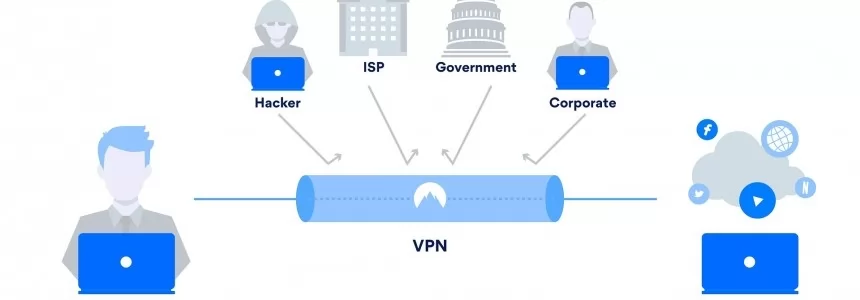
Browse safely and privately from your mobile phone using a VPN
Every day our smartphones suffer attacks, viruses, malware and information theft. In this article you will be able to deduce if you need a VPN in your mobile phone to safely surf the Internet, to avoid possible attacks on public Wi-Fi networks and also to filter out advertising and malware…
Category : Security 25-08-2020 by Janeth Kent
The concept of Model-View-Controller (MVC) explained
In software engineering, we use design patterns as reusable solutions to a commonly occurring problem, a pattern is like a template for how to solve a problem. Model-View-Controller (MVC) is a software design pattern that divides the related program or web application into three interconnected elements or components. Each of these…
Category : Programming 22-10-2020 by
Get ready for the future: What Does The Future Of SEO Look Like?
How will SEO change in 2030? There are various positions and assumptions that we can make about this so that you can think about the strategies to take when the future catches up with us. Anyone who works in SEO knows the great challenge of positioning a site on the web…
Category : Seo 19-08-2020 by Silvia Mazzetta
How to configure Tor to browse the deep web safely
Today we explain how to set up Tor to browse safely, and we'll share some links to safe sites on the deep web to get you started. Many already know that not everything on the Internet appears in Google, Yahoo, Bing or other search engines, and that accessing much of this…
Category : Security 12-08-2020 by Silvia Mazzetta
How to create the perfect hacker-proof password
We have not learned and we still use passwords that are extremely easy to hack and vulnerable to cyber attacks. If you don't want your credentials to end up in the hands of criminals or traded on the dark digital shelves of the Deep Web, we bring you a simple…
Category : Security 11-08-2020 by Silvia Mazzetta
What is the origin of the word SPAM?
It is 40 years since the first spam e-mail was sent. Surely most of the readers of this blog had not yet been born, as well as annoying mail with which we are bombarded in our emails, social networks, or mobiles already existed long before our existence. Have you ever wondered what the origin of the…
Category : Web marketing 03-08-2020 by Janeth Kent
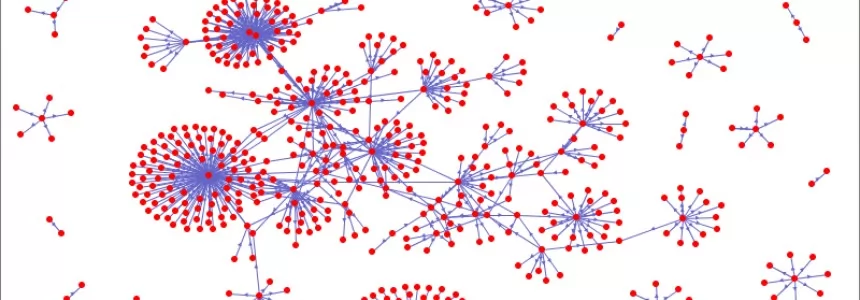
Introduction to Network Theory
Modern network theory was introduced at the end of the nineties by the PhD student Reka Albert and then monopolized by her tutor L.A. Barabasi, who made an empire out of it. The idea was not new, network theory is based on graph theory and graph theory had been already introduced…
Category : Networking 03-08-2020 by
Why is Website Performance Important for Online Businesses?
Your web is the site where most individuals will connect with your business. Your digital marketing processes will most probably send customers to your website. It might be to get information concerning your products and services, obtain contact information, or make purchases. Website performance, also known as web optimization, is a…
Category : Web marketing 24-07-2020 by Janeth Kent
Popular DNS Attacks and how to prevent them
DNS services are essential for web browsing. However, it is one of the most vulnerable to attacks. This guide will detail the most dangerous DNS attacks and some actions that will protect the network infrastructure. One of the reasons why DNS services have some susceptibility to attack is the UDP transport…
Category : Security 20-07-2020 by Silvia Mazzetta
TypeScript: The evolution of JavaScript
When you're involved in the development of a large project, programming languages like JavaScript don't seem to be the best solution. Their lack of elements such as Language Aids has created the need for code-friendly alternatives. Here we tell you about one of these options. TypeScript, is a project developed and…
Category : Javascript 18-07-2020 by Janeth Kent
How Learning Accents Connects Us To The World At Large
Accents are something we often only see in terms of region or a way of speaking. We don’t connect the ways in which they reflect on the cultures they serve or the people who speak them. In reality, where one lives, dictates how they speak and the words they use more than just about…
Category : Web marketing 16-07-2020 by Janeth Kent
Smishing: risks, examples and how to avoid it
Do you know what smishing is, what risks it involves and how you can avoid it? The cyber-criminals are betting on the technique known as Smishing when it comes to defrauding users through text messages (SMS). The objective of Smishing is the same as that of other types of scams…
Category : Security 16-07-2020 by Silvia Mazzetta
A collection of interesting networks and technology aiming at re-decentralizing the Internet
The decentralised web, or DWeb, could be a chance to take control of our data back from the big tech firms. So how does it work? Take a look at this collection of projects aimed to build a decentralized internet. Cloud BitDust - is decentralized, secure and anonymous on-line storage, where only…
Category : Networking 27-08-2020 by Janeth Kent
Awesome JavaScript Games and Js Software to create Games
Best sites js13kGames 2019 - Highlights from the js13kGames 2019 competition. js13kGames 2018 - 13 Games in ≤ 13kB of JavaScript. js13kGames 2017 - Build a game in 13kB or less with js13kGames. Adventure Triangle: Back To Home - You are lost in the cave. Try to get out and back to home. Sometimes it…
Category : Javascript 30-06-2020 by Janeth Kent
Parenting, pandemic and UX: Learning from design of experiences
After the quarantine, many of us have had to adapt our work and personal routines to the new remote paradigm. As a mother, I decided to share some things I've learned. We've been in total quarantine for weeks. Weeks in which we close the office and live and work in the 4…
Category : Ui/ux design 17-06-2020 by Silvia Mazzetta
Neumorphism (aka neomorphism) : new trend in UI design
This area, which arises from a basic human need, such as the urge to communicate, is constantly changing thanks to the advances of the technological era. Today, we invite you to reflect on the origin of this discipline and its future challenges. Graphic language has always been present throughout our lives…
Category : Ui/ux design 17-06-2020 by Silvia Mazzetta
Is JavaScript good for machine learning?
One of the things you always hear when you are talking to someone related to the M.L. world is that, one must learn Python because the vast majority of the major libraries are in that technology. You're probably right, but I chose JavaScript as the metal of my sword and…
Category : Javascript 16-06-2020 by Silvia Mazzetta
What is Machine Learning ?
Artificial Intelligence or AI is a trend in technology and has been the main topic of many philosophical debates as to where this field will lead us as humanity. This time I'm going to focus on a subfield of Artificial Intelligence that is Machine Learning, which I am currently very passionate…
Category : Technology 16-06-2020 by Silvia Mazzetta
Why do you vote the way you do in the age of misinformation and fake news?
In this context of the electoral campaign in which we are immersed, the 'political hoaxes' are becoming more relevant and it is expected that attacks to destabilize the parties and candidates in order to influence the electorate will increase. As recent examples, let's remember that disinformation campaigns influenced Trump to win…
Category : News and events 11-06-2020 by Silvia Mazzetta
What is Cyber Intelligence and how is it used?
What is Cyber-intelligence and what is it used for? This is a question that is usually asked by security, cyber-security and intelligence professionals. Cyber-intelligence is a hybrid concept between these three worlds and professional fields, and therefore it is an opportunity and a necessity to know what it is and what…
Category : Security 11-06-2020 by Silvia Mazzetta
SEO Mistakes that Need to Be Avoided
In today's digital age, search engine optimization (SEO) plays a critical role in determining the success of any online business. However, implementing SEO strategies can be complex, and mistakes are common. To ensure your website achieves optimal performance and ranks well on search engine result pages (SERPs), it is essential…
Category : Seo & sem 15-06-2023 by Janeth Kent
How to move Chrome, Firefox or Edge cache to save space
Caching is a technique used by many programs to improve their performance, especially for applications that run over the Internet, such as streaming programs or web browsers. This technique consists of saving all or part of the information being processed in a directory so that, if we return to it,…
Category : News and events 04-06-2020 by Janeth Kent
How beneficial is React Native for developing a mobile app?
A substantial alternative of cross-platform app development is fully native development. If you follow the approach of native mobile app development such as react native development company in Bangalore, you will be able to create separate ones for both Android as well as iOS. The framework of React Native is…
Category : Javascript 02-06-2020 by Luigi Nori
How to Take Your Small Ecommerce Business to the Next Level
Running an ecommerce business can be both exciting and financially rewarding. However, as you increase your customer base, it might seem difficult to successfully scale your operations. If your site is growing in popularity, or you want to attract more customers to your online venture, read the below top tips on…
Category : Web marketing 25-01-2022 by Janeth Kent
How to save and edit photos in WebP format in GIMP
GIMP (GNU Image Manipulation Program) is a powerful open-source image editing software that provides a wide range of features and tools. While GIMP initially lacked native support for WebP format, the latest versions have integrated WebP support, making it easier than ever to save and edit photos in this efficient…
Category : Web design 29-05-2023 by Silvia Mazzetta
How to enable Chrome's new feature that blocks ads that consume your CPU, battery, and Internet connection
Google has announced that it will begin experimenting with a technology that they have been developing for months, in order to improve the battery consumption of our computers and the speed of the pages we visit. In a blog post, the company announced that it plans to integrate it into Google…
Category : News and events 17-05-2020 by Silvia Mazzetta
Introduction to BEM (Block Element Modifier)
Problems with naming CSS classes I think I might not be the only one with this experience: after finally grasping all the important concepts regarding CSS I wanted to start giving what I thought would be beautiful yet simple style to my HTML code. But suddenly I ended up with class…
Category : Css 23-05-2020 by Iveta Karailievova
Xiaomi's high-tech masks: they disinfect themselves and work with your mobile phone's facial recognition
At this point in the pandemic, we have all become experts on masks to deal with the coronavirus outbreak. There are masks that protect you, that protect others, that last a few hours, that are single-use... and now there are also masks that are self-disinfecting and that also work with the…
Category : Technology 10-05-2020 by Silvia Mazzetta
How to Change Your DNS Server (And Why You Should)
It's so easy to connect to the internet that you don't think much about how it actually works. You've likely heard about things like IP address, ethernet, DNS servers, or similar terms. They often come up when you try to diagnose internet problems on your home network. Though, this time…
Category : Networking 09-05-2020 by Luigi Nori
Web shells as a security thread for web applications
Over the past two decades, web applications as an alternative to traditional desktop application have been on to rise. As their name suggests, they are installed on web servers and accessed via a web browser. This gives web apps a rather long list of advantages: multi-platform cross-compatibility, no installation required for…
Category : Security 04-05-2020 by Iveta Karailievova
Protect yourself: know which apps have access to your location, microphone and camera
When you install an application on your smartphone, you decide what permissions you give it, but it's not always clear. We tell you how to know if those permissions are too much... Smartphones have become the target of choice for hackers and criminals who want to make money or extort money…
Category : News and events 20-04-2020 by Silvia Mazzetta
JavaScript Development Services and How It Works
JavaScript is a programming language. This scripting language, however, is used to create features on web pages. As a result, it helps to make web pages alive. All that stuff that you see or do on the internet or websites or web applications is because of JavaScript. It is used to…
Category : Javascript 17-04-2020 by Luigi Nori
The best websites of the Tor Deep Web and Dark Web Network
We already talked about Deep Web more than a year ago, explaining that to open Deep Web (or rather Dark Web) sites you need total and undetectable user anonymity and access to the "onion" network. The Dark Web is much smaller than the Deep Web and is composed mainly of sites…
Category : Security 03-11-2022 by Janeth Kent
The exciting story of JavaScript (in brief)
Javascript is a client-side programming language that has changed the Internet as we know it today. The term "client side" means that it runs on our web browser without the need for a web hosting. Along with html and css it is one of the 3 pillars of web design. It is…
Category : Javascript 13-04-2020 by Silvia Mazzetta
5 Fool-Proof Ideas For Location-Based Apps
Like it or not, geolocation is a part of our everyday lives. In fact, you’ll find the technology pre-installed on 90% of the apps currently living on your smartphone. Location-based apps are here to stay, which makes them a lucrative option for mobile app developers looking to take advantage of…
Category : Software 01-04-2020 by Luigi Nori