results for: real
The man who married a hologram: fact or fiction? The story of Akihiko Kondo
His name is Akihiko Kondo, he is 38 years old, and four years ago he married Hatsune Miku. What's strange about this? Miku is not a person but a hologram that 'lives' in a device called the Gatebox. Let's take a look at the details of this controversial yet interesting…
Category : News and events 19-07-2022 by Janeth Kent
8 benefits of having a website for your business
At this moment, the Internet is a phenomenon that is sweeping the world. It has been able to interconnect millions of users all over the planet. People have made the Internet an indispensable part of their lives. If they want to find out where to eat, they look on their…
Category : Web marketing 03-06-2022 by Nadal Vicens
Open source web design tools alternatives
There are many prototyping tools, user interface design tools or vector graphics applications. But most of them are paid or closed source. So here I will show you several open source options for you to try and use the one you like the most. Penpot Penpot is the first open source design…
Category : Web design 03-06-2022 by Nadal Vicens
How to Start a Web Design Agency in 2022
If the last two years have shown us anything, it’s that a good online presence is paramount to success in the modern world of business. Once they have a robust web-based reputation in place, companies have the capacity to disrupt their sectors in an engaging, intuitive, and ultimately profitable fashion.…
Category : Web marketing 25-01-2022 by Janeth Kent
Node.js and npm: introductory tutorial
In this tutorial we will see how to install and use both Node.js and the npm package manager. In addition, we will also create a small sample application. If you have ever used or thought about using a JavaScript-based development tool, you have probably noticed that you need to install…
Category : Javascript 05-11-2021 by Silvia Mazzetta
How to set up your own free web server with XAMPP
Nowadays anyone can create their own website easily and free of charge. Whether through a CMS (such as WordPress) or by hand with HTML, CSS and JavaScript, in a few minutes we can have a more or less functional website up and running. However, in order to test that everything…
Category : Servers 25-10-2021 by Silvia Mazzetta
Secret iPhone codes to unlock hidden features
We love that our devices have hidden features. It's fun to learn something new about the technology we use every day, to discover those little features that aren't advertised by the manufacturer. And unless you spend a lot of time playing around in the Phone app, you probably don't know, until…
Category : Security 22-10-2021 by Silvia Mazzetta
How to access webcam and grab an image using HTML5 and Javascript
We often use webcams to broadcast video in real time via our computer. This broadcast can be viewed, saved and even shared via the Internet. As a rule, we need software to access the webcam and stream video. But you can also stream video on websites without using third-party software. The…
Category : Javascript 20-05-2021 by Janeth Kent
Advanced Android tutorial: discover all your phone's secrets
It is highly probable that you are not taking advantage of even half of the potential that your Android device has to offer. These small pocket computers, which we call smartphones, have increasingly advanced and powerful hardware that, together with the possibilities offered by an operating system as flexible as…
Category : Mobile 06-05-2021 by Janeth Kent
Top Javascript Libraries and Frameworks Part 2
What are JavaScript frameworks? JavaScript frameworks are application frameworks that allow developers to manipulate code to meet their particular needs. Web application development is like building a house. You have the option of creating everything from scratch with construction materials. But it will take a long time and can incur high costs. But…
Category : Javascript 06-05-2021 by Janeth Kent
How to Send Email from an HTML Contact Form
In today’s article we will write about how to make a working form that upon hitting that submit button will be functional and send the email (to you as a web creator and to the user or customer as well). If you’re a PHP developer, there's a high probability that you…
Category : Programming 10-05-2021 by
Top JavaScript libraries and frameworks part 1
JavaScript libraries and frameworks make it easy to develop websites and applications with a wide variety of features and functionality, all with dynamic, flexible and engaging features. According to a 2020 StackOverflow survey, JavaScript remains the most widely used programming language (for the eighth year), with 67.7% of respondents using it. Its…
Category : Javascript 06-05-2021 by Janeth Kent
Network attacks and how to avoid them
Nowadays it is impossible to list all the different types of attacks that can be carried out on a network, as in the world of security this varies continuously. We bring you the most common ones according to the network attack databases, so that we can keep up to date…
Category : Security 03-05-2021 by Silvia Mazzetta
Looping through a matrix with JavaScript
We were already talking about how to multiply arrays in JavaScript and we realised that we had not explained something as simple as traversing an array with Javascript. So we couldn't let the time pass and we have started working to explain you how to do this task. The first thing…
Category : Javascript 03-05-2021 by Janeth Kent
How to set up your Android phone: learn how to get your new phone up and running
If you've just bought a great new Android phone, you'll want to start using it as soon as possible. You'll see that it's not hard to get the initial set-up and configuration to get it ready to use, and we'll guide you every step of the way. From connecting your Google account,…
Category : Mobile 28-04-2021 by Janeth Kent
5 Terrific iOS-Friendly Canva Alternatives to Upgrade Your Marketing Visuals
Sometimes you want to use your iPhone to create compelling, engaging marketing visuals, and as awesome as Canva is, many of us are interested in seeing what other options are out there. As all marketers know, consistent branding is a must for any company (or even individual) who wants to stand…
Category : Web marketing 05-05-2021 by Janeth Kent
Top tools for UX design and research
This article is a compilation of the "ux tools" I have tested in recent years. I've separated the tools by categories, although I recommend you to take a look at all of them, you might find some you didn't know. - Conceptualisation and project management tools - UX testing and research tools - Analytics…
Category : Ui/ux design 23-04-2021 by Silvia Mazzetta
The best free tools to Transcribe audio to text
With this article we bring you a list of the best tools for transcribing audio to text, offering you some that simply do it with dictated audio, but also others capable of loading audio files. The collection is varied, and we have mobile applications, web pages, and computer programs capable…
Category : Software 15-04-2021 by Janeth Kent
SEO: How to choose the best Anchor Text
Anchor Text are the words used to insert a link within a piece of content. This text can be anything from "click here" to the name of a brand or even a series of keywords or phrases. When choosing the best anchor text, always put the user experience first. Since the launch…
Category : Seo & sem 15-03-2021 by Janeth Kent
Elon Musk To Found Starbase, A City In Texas To House His Companies And Projects
Elon Musk's initiatives hardly go unnoticed, either because of how curious, innovative and/or eccentric they can be. Recently, SpaceX's CEO confirmed that it is getting into a new business: building cities. An announcement of few words that generated a lot of buzz. Lately, Elon Musk has opted for terse messages on Twitter, playing…
Category : Technology 05-03-2021 by Janeth Kent
Bootstrap 5 beta2. What offers?
Since the release of the Bootstrap 4 is three years, in this article we will present what is new in the world’s most popular framework for building responsive, mobile-first sites. If you want to know what are the significant changes that come with the next version 5 which is in…
Category : Css 05-04-2021 by
Top Graphic Design e-Books & How to Get them on Your iDevice
Ma-no.org may include links to commercial websites. A commercial website is defined as a business site designed to generate income through the provision of services and products. Where links to commercial sites are included on ma-no.org, this does not indicate or imply any affiliation or endorsement between that commercial entity…
Category : Ui/ux design 03-03-2021 by Luigi Nori
Cybersecurity and Data Privacy: Why It Is So Important
The internet has made it very easy for people all across the world to stay connected with one another. Access to information, services, and people is possible for pretty much anyone with an internet connection today. But while this has brought many positive changes to how people live and connect,…
Category : Security 26-02-2021 by Janeth Kent
Top 7 Potential Tools for Automation Testing
Today's digital economy has significantly changed how organizations deliver products and services. Many organizations are gravitating towards smart methodologies and automated tools to spark customer interest in their products and increase revenue to ensure quality and speedy deliveries. These testing tools help organizations to determine the expected and actual product delivery…
Category : Web marketing 12-02-2021 by Janeth Kent
Interesting and Helpful Google Search Features You’ll Want to Start Using
Google – THE search engine for many internet users. It has been with us since its launch back in 1998 and thanks to its simplicity of use and genius algorithms, it grew so popular, that most of us cannot imagine our day-to-day life without it. Many petty arguments between friends…
Category : Software 31-01-2021 by Iveta Karailievova
Graphic design and its impact on Web Development
In today's article we will explain the concept of graphic design, its fundamentals and what it brings into web development. Graphic design is applied to everything visual, believe or not, it can aid in selling a product or idea, it's applied company identity as logos, colors, typography of the company…
Category : Web design 05-04-2021 by
Deepfakes Detection – An Emerging Technological Challenge
It is highly probable that while browsing the Internet, everyone of us has at some point stumbled upon a deepfake video. Deepfakes usually depict well-known people doing really improbable things – like the queen of England dancing on her table or Ron Swanson from Parks and Recreations starring as every…
Category : Technology 27-01-2021 by Iveta Karailievova
Cumulative Layout Shift, what is and How to optimize CLS
Cumulative Layout Shift, one of the new Core Web Vitals metrics, is the first metric that focuses on user experience beyond performance. Unexpected movement of web page content is a major source of irritation for users on the web. The new cumulative design change metric helps developers understand the impact of…
Category : Seo & sem 14-01-2021 by Luigi Nori
7 Astonishing New Uses of Machine Learning
Recently a strange video published on YouTube caused a controversy – it was a funny take on Queen Elizabeth’s traditional Christmas message created by Channel 4, a British public-service television broadcaster. They used AI to produce a fake video of the Queen making it look very realistic and if the message itself…
Category : Technology 31-12-2020 by Iveta Karailievova
Validating HTML forms using BULMA and vanilla JavaScript
Today we are going to write about contact forms and how to validate them using JavaScript. The contact form seems to be one of the top features of every basic home page. It is a great way to encourage your visitors to make contact with you, by adding a form which…
Category : Javascript 31-12-2020 by
What is Django and what is it used for
When we talk about Django, we refer to that framework that is used for any totally free and open source web application which is written in Python. Basically, it's a group of elements that will help you create web pages much more easily and quickly. At the moment you are going…
Category : Programming 26-12-2020 by Janeth Kent
SEO: How to find and remove artificial links
At Ma-no we are aware of the importance of a good linkbuilding strategy in order to achieve success with a website. Links are key to placing a website among the top positions in Google search results, and therefore increasing the number of visits and conversions. But in today's post we are not…
Category : Seo & sem 23-12-2020 by Silvia Mazzetta
Dark Web: the creepy side of the Internet is not as dark as believed
People who surf the Dark Web are not necessarily looking for something illegal. Most people want to protect their privacy. And according to a recent study, 93 percent only use websites that are freely accessible. It is almost impossible not to leave traces on the Internet and therefore reveal a lot…
Category : Security 17-05-2023 by Silvia Mazzetta
Some Neat Ways to Improve Your Internet Browsing Experience?
Not everyone has the best time when they are surfing the net. There are multiple reasons why an internet browser struggles, but that does not mean the situation is out of your hands. Relying on the internet is inevitable these days. We use it for work, entertainment, and socializing with friends…
Category : News and events 21-12-2020 by Janeth Kent
Python or Swift: Revealing Benefits and Drawbacks of Each Language and Their Differences
Programming languages constantly evolve to improve software performance and simplify developers’ lives. That’s why the programming languages’ ranking is so unstable. Popular languages change every year. While some become outdated and uninterested due to poor features, others get ahead of the ranking because of frequent updates and outstanding performance. There…
Category : Programming 04-03-2021 by
Install MacOS on PC - the Ultimate Guide (Hackintosh)
There has always been a belief that the Apple MacOS Operating System could only be installed on computers sold directly by Apple. But on the Internet there is a large community dedicated to Hackintosh. And in this guide we are going to show you today all you need to know…
Category : Operating systems 10-12-2020 by
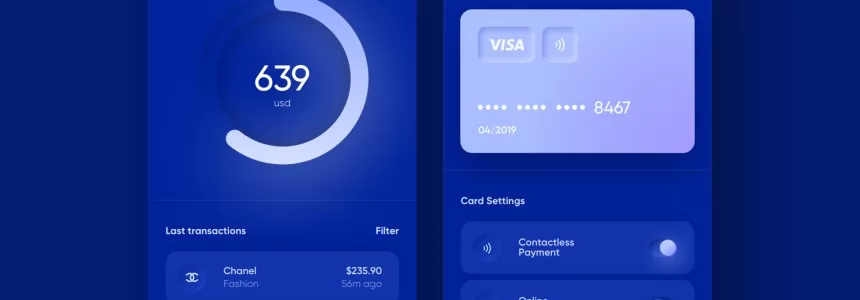
How to Use Bitcoin: mining, wallets, payments
You have certainly heard of Bitcoin, the virtual currency that periodically makes people talk about itself because of its innovative and particular nature. In this case, you have probably also wondered how it is possible to get and subsequently spend Bitcoins, and if it is something useful, as well as…
Category : Technology 10-12-2020 by Silvia Mazzetta
A Java approach: While loop
Hello everyone and welcome back! After having made a short, but full-bodied, introduction about cycles, today we are finally going to see the first implementations that use what we have called preconditional cycle. In Java, as in many other programming languages, this type of cycle is translated with the term while, which…
Category : Java 25-10-2020 by Alessio Mungelli
Website Traffic Getting Low? 4 Immediate Action to Take
If you have created a website, I am sure your end objective is to create a strong brand presence, boost engagement, and multiply revenue. An interesting statistic showed that there were 22.31 million internet users at the start of the year, in Australia. This means that there are ample opportunities to…
Category : Web marketing 04-12-2020 by Luigi Nori
Google everywhere: anatomy of a massive giant
The alarm clock is going off. A hand floats over the bedside table groping for the source of the sound: probably a cell phone and maybe one of the more than 2.5 billion Android devices in the world. Alphabet's operating system (Google's matrix) concentrates 74.6% of the market and together with…
Category : Technology 03-12-2020 by Silvia Mazzetta
Making AJAX requests to a REST API using vanilla JavaScript and XHR
Imagine you just build your first static web page and you would like to add some functionality to make it more attractive and generally more usable. Perhaps you would like to entertain your web page visitor with randomly generated cat facts, jokes, or, (preferably not randomly generated) weather forecasts or…
Category : Javascript 25-11-2020 by Iveta Karailievova
The BleedingTooth vulnerability and other Bluetooth security risks
Have you ever heard of BleedingTooth? And we do not mean the really disturbing looking mushroom which goes by this name and is totally real (we double checked) but one of the lately discovered vulnerabilities in Linux systems. It had hit the tech news recently, when Andy Nguyen, a Google security…
Category : Security 10-11-2020 by Iveta Karailievova
A Java approach: The Cycles - Introduction
Hello everyone and welcome back! Until now, we have been talking about variables and selection structures, going to consider some of the fundamental aspects of these two concepts. Theoretically, to write any kind of program, the notions seen so far might be sufficient. However, a problem arises. How can we…
Category : Java 23-10-2020 by Alessio Mungelli
A Java Approach: Selection Structures - Use Cases
Hello everyone and welcome back! Up to now we have been concerned to make as complete an overview as possible of the fundamental concepts we need to approach the use of conditional structures. We have therefore introduced the concept of conditional structures, outlining the various situations that could arise. We…
Category : Java 20-10-2020 by Alessio Mungelli
JavaScript: Spread and Rest operators
In today’s article we are going to talk about one of the features of the ES6 version(ECMAScript 2015) of JavaScript which is Spread operator as well as Rest operator. These features may be very useful when developing and working with front-end frameworks. We will explain how you can use it in…
Category : Javascript 05-04-2021 by
Why You Should Hire Node.js Developer for Your Backend Development
When developers are building a new website, they mainly focus on both frontend and backend development. The frontend code helps create the interfaces through which the app interacts with the users while the back-end code interacts with the server to deliver data or content that is displayed to the website…
Category : Javascript 27-10-2020 by Luigi Nori
How to watch deleted or private Youtube videos
Today we are going to talk about the technique which you permit to be able to recover videos from Youtube that was deleted, made private or simply blocked by Youtube itself. With this trick you most of the time would do just that. How is this possible we will explain…
Category : Social networks 05-04-2021 by
GAN Generated Images
Let’s play a game - can you guess what these portraits have in common? They all depict non-existent people. All these images were created by artificial intelligence. We could say, that AI “dreamed” those people up. How can a machine make up people’s faces? The genius idea came from Ian Goodfellow, who was…
Category : Technology 28-10-2020 by Iveta Karailievova
A Java approach: conditional structures
Hello everyone and welcome back! The previous times we have introduced the concept of variable, trying to define some basic concepts about it. However, some situations suggest that the concept of variable alone is not enough to solve all the possible situations that may arise in front of us. A very…
Category : Java 03-04-2023 by Alessio Mungelli
3 awesome ways technology is helping us combat the COVID pandemic
Times are hard now, that humanity once more stumbled into a terrible pandemic. But in comparison to the poor folks back in 1918 when the Spanish flu was on wreaking havoc, nowadays we have the advantage of cutting edge technology on our side. Here’s a quick list of top three ways…
Category : Technology 28-10-2020 by Iveta Karailievova
How to Deal with Unnatural Inbound Links
A website that has a good rank on search engines, especially Google is a big task. Backlinks or Inbound links are one of the best ways to achieve this ranking. Sometimes in a haste to achieve this goal, websites indulge in underhanded behaviour like unnatural inbound links. These are considered…
Category : Seo & sem 25-10-2020 by Janeth Kent
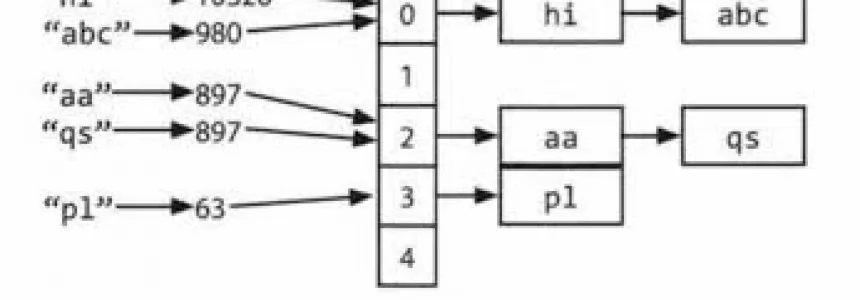
Hashmap: hashing, collisions and first functions
Today we are going to study some concepts closely related to hashmaps. The concepts we are going to see are hashing and collisions. Hashing The idea of hashing with chaining is to create a sort of array of lists, into which the elements are somehow inserted. We need to map the keys to…
Category : C language 28-06-2020 by Alessio Mungelli
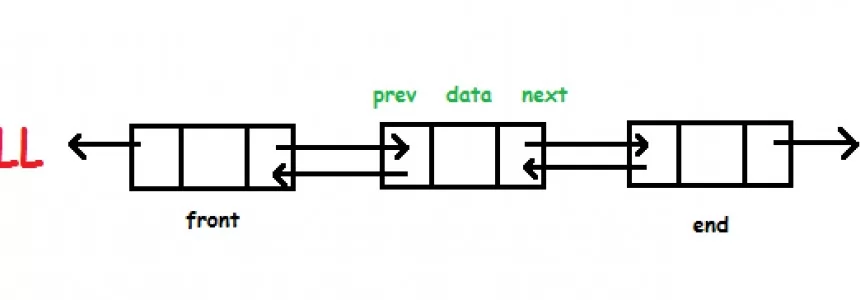
Hashmap: Overflow Lists
In this short series of articles we will go to see how it is possible to create the Hashmap data structure in C. In the implementation we're going to use the doubly concatenated lists as auxiliary data structures. Let's look at a possible implementation. Header file Let's first have a look to what…
Category : C language 18-06-2020 by Alessio Mungelli
A Java approach: variables - use case
Hello all friends and welcome back! After the introduction made on the variables, we try to analyse some critical issues that may arise in quite common situations. Let's start by analysing some practical examples. Example 1: division that returns a non-integer result The first critical case that might arise for those who approach…
Category : Java 22-10-2020 by Alessio Mungelli
A Java approach: variables
Hello everyone and welcome back! Today we will begin a journey that will lead us to study, and possibly review, what are the basics of programming. We will start by talking about variaibli. Introduction Anyone who wants to approach the world of programming will soon realise that coding is not exactly like what…
Category : Java 20-09-2020 by Alessio Mungelli
The new features coming to the Google search engine in autumn 2020
Google has included important improvements in its search engine, applying Artificial Intelligence, to make it easier for users to find what they are looking for. It has also announced new features in Google Lens and other search tools. The main novelties are the following: Many of the announced improvements involve the…
Category : Seo & sem 18-10-2020 by Luigi Nori
MAME Multiple Arcade Machine Emulator: How to download and configure this arcade emulator for Windows
Despite the fact that new state-of-the-art computer games are coming out every so often, the whole retro theme is very appealing to users who are looking to relive the long hours spent in front of a console, such as the NES or SNES, and even in arcades playing arcade machines.…
Category : Software 14-10-2020 by Luigi Nori
How to turn an Android device into a retro game console
If you like retro games and you want to set up your own system at home, a good way to do it is using Android. From emulators for Mega Drive, N64, GBA, PS1 or Super Nintendo, to other systems such as MAME, all of them are available in Android app…
Category : Software 14-10-2020 by Silvia Mazzetta
Network and port scanning with Zenmap
This article goes out to all the computer nerds who are, when it comes to networking, more on the noob-side of the crowd. It does not have to be complicated and everyone with patience and eagerness to learn something new can relatively quickly gain the knowledge necessary to feel more…
Category : Security 08-10-2020 by Iveta Karailievova
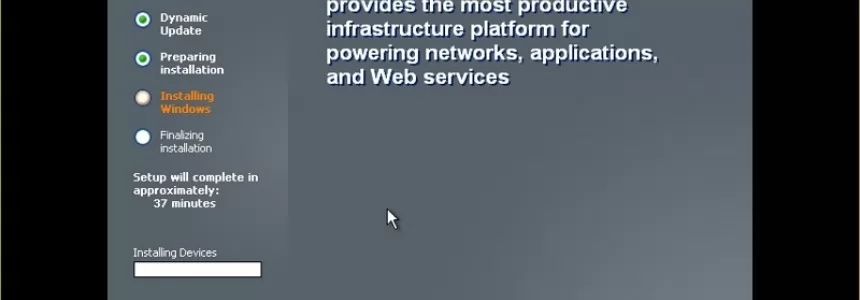
A Dev compile and install Windows XP and Server 2003 from filtered source code
One of the events in the IT field this year was the massive leak of the source code of Windows XP and other large systems such as Windows Server 2003. Although Microsoft has not yet pronounced on the veracity of the code, researchers say it seems real, and those who…
Category : Operating systems 08-10-2020 by Luigi Nori
HTTP Cookies: how they work and how to use them
Today we are going to write about the way to store data in a browser, why websites use cookies and how they work in detail. Continue reading to find out how to implement and manage them - if you're looking for code! Understanding HTTP COOKIES - What are they? Cookies and other types…
Category : Programming 27-11-2020 by
SEO in Google News: How to appear in Google News
Google News is a tool, from Google, that spreads current, reliable and truthful content from different websites or portals dedicated exclusively to news. The sites that appear in Google News have a great opportunity to increase traffic to your website and consequently the opportunity to increase your sales through it. If you…
Category : Seo & sem 26-06-2023 by Luigi Nori
Google Dorks: How to find interesting data and search like hacker
Go the words Google and Hacking together? Well if you thought that we will learn how to use hack Google, you might be wrong. But we can Use Google search engine to find interesting data accidentally exposed to the Internet. Such a simple search bar has the potential to help you also…
Category : Security 03-12-2021 by
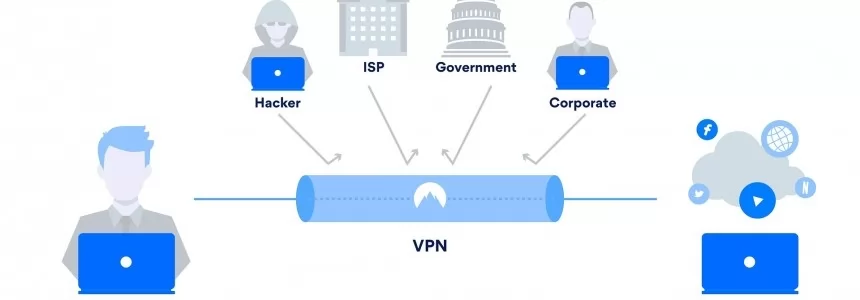
Double VPN: what it is and how it works
Privacy on the web is a very important factor for users and there are more and more tools to help us maintain it. Without a doubt VPN services have had a very important increase in recent times and represent an option to preserve our data when we browse. However, in…
Category : Security 28-09-2020 by Silvia Mazzetta
Data Scraping and Data Crawling, what are they for?
Right now we are in an era where big data has become very important. At this very moment, data is being collected from millions of individual users and companies. In this tutorial we will briefly explain big data, as well as talk in detail about web crawling and web scraping…
Category : Web marketing 25-09-2020 by Silvia Mazzetta
How to write our own Privacy Policy
In this article we will talk about Privacy Policy statements, how you can write one and implement it on your page. Why did it pop up? These days when we browse on any new page, or when we visit the site for the first time, most of the time we have to…
Category : Development 13-12-2023 by
How to securely access the Dark Web in 15 steps. Second part
Let's continue with the 2nd part of our article in which we try to give you some advice on how to safely and securely explore the dark web. Let's restart from number 6. 6. Changes the security level in the Tor browser It is also possible to increase the security level of the…
Category : Security 08-03-2024 by Janeth Kent
How to securely access the Dark Web in 15 steps. First part
The dark web can be a pretty dangerous place if you don't take the right precautions. You can stay relatively safe with a good antivirus and a decent VPN. However, if you want to be completely anonymous and protect your device, you'll need a little more than that. Here there are…
Category : Security 08-03-2024 by Silvia Mazzetta
How to Browse the Internet Anonymously: 6 tips
Most of the actions you take online are not as private as you might imagine. Nowadays, countless people and groups try to follow our online behaviour as closely as possible. Our ISPs, our network administrators, our browsers, search engines, the applications we have installed, social networks, governments, hackers and even the…
Category : Security 16-09-2020 by Silvia Mazzetta
Mobile cryptophones on the market (legals)
As we have said, it is a market often at the borders of legality, also because these devices are particularly used by criminals. Some models, however, are also available through standard commercial channels, while others are sold through direct distributors and cash payment. We list some of them here, with the…
Category : Security 15-09-2020 by Silvia Mazzetta
What is a Cryptophone and how it works
The so-called cryptophones, are anti-interception smartphones as they use encryption methods to protect all communication systems. Here are all the details and the truth about these "unassailable" phones. The recent Encrochat affair, recently investigated for illegal activities, has brought to light the so-called cryptophones. They are smartphones - legal in themselves -…
Category : Security 11-09-2020 by Silvia Mazzetta
How to comply with Google's quality guidelines in 2020
Google provides a set of guidelines on what your website's content should look like in order to appear in search results. There are several categories within the Google guidelines: Webmaster Guidelines. General guidelines. Content-specific guidelines. Quality guidelines. In this article we will focus on the Quality guidelines. Quality guidelines, describe techniques whose use is prohibited and which,…
Category : Seo & sem 09-09-2020 by Silvia Mazzetta
How are businesses using artificial intelligence?
The term Artificial Intelligence (AI), "the intelligence of the machines", unifies two words that, a priori, could not be associated, since the term intelligence is attributed to the faculty of the mind to learn, to understand, to reason, to take decisions and to form a determined idea of the reality. How…
Category : News and events 21-06-2023 by Silvia Mazzetta
What cybersecurity professionals have learned from the lockdown experience
The COVID-19 pandemic has radically changed the rules of the game for most companies and individuals in a very short time; it has also changed the international computing universe. Sudden changes in people's habits as well as in business operations have altered some of the elements that characterize cyber-risk. And…
Category : Security 26-08-2020 by Silvia Mazzetta
Matrix. An open network for secure and decentralized communication that you can install in your Ubuntu server
Imagine to have an open platform that is as independent, vibrant and evolving as the Web itself, but for communication. As of June 2019, Matrix is out of beta, and the protocol is fully suitable for production usage. But, what is Matrix? Matrix is an open standard for real-time, interoperable and decentralized communication over…
Category : Networking 25-08-2020 by Luigi Nori
Browse safely and privately from your mobile phone using a VPN
Every day our smartphones suffer attacks, viruses, malware and information theft. In this article you will be able to deduce if you need a VPN in your mobile phone to safely surf the Internet, to avoid possible attacks on public Wi-Fi networks and also to filter out advertising and malware…
Category : Security 25-08-2020 by Janeth Kent
The 6 Essentials for Creating a Visually Appealing Web Design
Creating a website might seem like a simple thing. After all, what do you really need besides a good hosting provider and relevant content, right? Well, the reality is quite different. Things might have worked like that in the past, but they are quite different now. The internet is advancing, and…
Category : Web design 25-08-2020 by Silvia Mazzetta
How to configure Tor to browse the deep web safely
Today we explain how to set up Tor to browse safely, and we'll share some links to safe sites on the deep web to get you started. Many already know that not everything on the Internet appears in Google, Yahoo, Bing or other search engines, and that accessing much of this…
Category : Security 12-08-2020 by Silvia Mazzetta
What is the origin of the word SPAM?
It is 40 years since the first spam e-mail was sent. Surely most of the readers of this blog had not yet been born, as well as annoying mail with which we are bombarded in our emails, social networks, or mobiles already existed long before our existence. Have you ever wondered what the origin of the…
Category : Web marketing 03-08-2020 by Janeth Kent
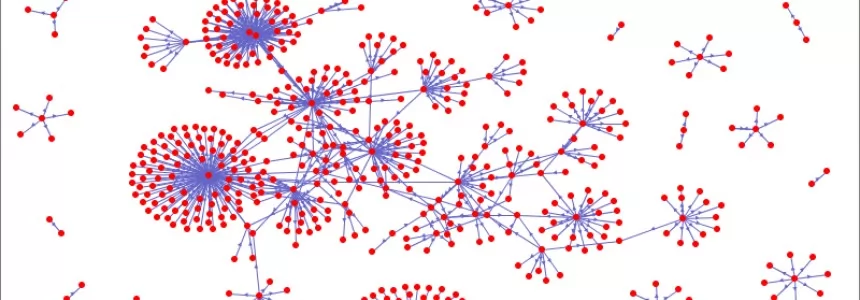
Introduction to Network Theory
Modern network theory was introduced at the end of the nineties by the PhD student Reka Albert and then monopolized by her tutor L.A. Barabasi, who made an empire out of it. The idea was not new, network theory is based on graph theory and graph theory had been already introduced…
Category : Networking 03-08-2020 by
7 Killer Strategies to Increase Your Sales Funnel Conversion Rates
Have you been using online sales funnels to grow your business online but it hasn't really worked for you? There's something you are not doing right. Use these strategies to make your sales funnels convert better. We are living in a competitive digital era, and as an entrepreneur, you have to…
Category : Web marketing 23-07-2020 by Janeth Kent
Why is Website Performance Important for Online Businesses?
Your web is the site where most individuals will connect with your business. Your digital marketing processes will most probably send customers to your website. It might be to get information concerning your products and services, obtain contact information, or make purchases. Website performance, also known as web optimization, is a…
Category : Web marketing 24-07-2020 by Janeth Kent
Popular DNS Attacks and how to prevent them
DNS services are essential for web browsing. However, it is one of the most vulnerable to attacks. This guide will detail the most dangerous DNS attacks and some actions that will protect the network infrastructure. One of the reasons why DNS services have some susceptibility to attack is the UDP transport…
Category : Security 20-07-2020 by Silvia Mazzetta
How Learning Accents Connects Us To The World At Large
Accents are something we often only see in terms of region or a way of speaking. We don’t connect the ways in which they reflect on the cultures they serve or the people who speak them. In reality, where one lives, dictates how they speak and the words they use more than just about…
Category : Web marketing 16-07-2020 by Janeth Kent
Bank phishing by email: best way to prevent it
No one is safe from Pishing attacks, especially bank Phising. Large and small companies in all industries are being attacked repeatedly. Phishing is so popular with cybercriminals because it provides them with access to the most vulnerable part of any network: the end users. Bank Phishing is increasingly being used…
Category : Security 16-07-2020 by Silvia Mazzetta
7 Most Effective Ways to Make Money From Photography
Many people all over the world enjoy photography. At first, it may seem difficult to learn, but once you turn it into a hobby, then it becomes a pleasure rather than a difficulty. And the better you get with photography, the more you understand and want to invest in better…
Category : News and events 15-07-2020 by Janeth Kent
Smishing: risks, examples and how to avoid it
Do you know what smishing is, what risks it involves and how you can avoid it? The cyber-criminals are betting on the technique known as Smishing when it comes to defrauding users through text messages (SMS). The objective of Smishing is the same as that of other types of scams…
Category : Security 16-07-2020 by Silvia Mazzetta
A collection of interesting networks and technology aiming at re-decentralizing the Internet
The decentralised web, or DWeb, could be a chance to take control of our data back from the big tech firms. So how does it work? Take a look at this collection of projects aimed to build a decentralized internet. Cloud BitDust - is decentralized, secure and anonymous on-line storage, where only…
Category : Networking 27-08-2020 by Janeth Kent
Facebook, three questions to recognize fake news (and not share it)
Where's it coming from? What's missing? How do you feel? These are the three questions that Facebook recommends to all users to ask themselves before sharing news. The initiative is part of the fight against fake news undertaken by Mark Zuckerberg's popular social network which - during the pandemic -…
Category : Social networks 02-07-2020 by Janeth Kent
Awesome JavaScript Games and Js Software to create Games
Best sites js13kGames 2019 - Highlights from the js13kGames 2019 competition. js13kGames 2018 - 13 Games in ≤ 13kB of JavaScript. js13kGames 2017 - Build a game in 13kB or less with js13kGames. Adventure Triangle: Back To Home - You are lost in the cave. Try to get out and back to home. Sometimes it…
Category : Javascript 30-06-2020 by Janeth Kent
Neumorphism (aka neomorphism) : new trend in UI design
This area, which arises from a basic human need, such as the urge to communicate, is constantly changing thanks to the advances of the technological era. Today, we invite you to reflect on the origin of this discipline and its future challenges. Graphic language has always been present throughout our lives…
Category : Ui/ux design 17-06-2020 by Silvia Mazzetta
Dark Web: how to access, risks and contents
You've probably heard of the Dark Web before, but do you really know what the Dark Web is, or what it consists of? Do you know its risks? Which users use the Dark Web? What content is published? Would you know how to access the Dark Web safely? If you are reading…
Category : Security 13-06-2020 by Silvia Mazzetta
Why do you vote the way you do in the age of misinformation and fake news?
In this context of the electoral campaign in which we are immersed, the 'political hoaxes' are becoming more relevant and it is expected that attacks to destabilize the parties and candidates in order to influence the electorate will increase. As recent examples, let's remember that disinformation campaigns influenced Trump to win…
Category : News and events 11-06-2020 by Silvia Mazzetta
Step by Step Guide to Successful Social Media Marketing
The most popular social media platforms boast of having hundreds of millions of active users every month. The number itself is more than enough to attract brands in trying to establish themselves as niche authorities on as many different social media websites as they can. If you are still relatively new…
Category : Web marketing 16-05-2023 by Silvia Mazzetta
How to turn your smartphone into a webcam for your pc
With the propagation of Covid-19 we all had to adapt to a new quarantine situation at home, and since the human being needs to communicate constantly, we used the internet channel to make group calls, be it between friends or business meetings. This has led to a rapid expansion of online…
Category : Multimedia 17-05-2020 by Luigi Nori
Introduction to BEM (Block Element Modifier)
Problems with naming CSS classes I think I might not be the only one with this experience: after finally grasping all the important concepts regarding CSS I wanted to start giving what I thought would be beautiful yet simple style to my HTML code. But suddenly I ended up with class…
Category : Css 23-05-2020 by Iveta Karailievova
Xiaomi's high-tech masks: they disinfect themselves and work with your mobile phone's facial recognition
At this point in the pandemic, we have all become experts on masks to deal with the coronavirus outbreak. There are masks that protect you, that protect others, that last a few hours, that are single-use... and now there are also masks that are self-disinfecting and that also work with the…
Category : Technology 10-05-2020 by Silvia Mazzetta
How to Change Your DNS Server (And Why You Should)
It's so easy to connect to the internet that you don't think much about how it actually works. You've likely heard about things like IP address, ethernet, DNS servers, or similar terms. They often come up when you try to diagnose internet problems on your home network. Though, this time…
Category : Networking 09-05-2020 by Luigi Nori
Seo: How Search Behavior Has Changed During COVID-19 Pandemic
Google positioning is experiencing a before and after with the coronavirus crisis. The way we search in Google has changed; The way Google the search engine gives us the results has changed ; The tools that webmasters have at their disposal have changed. Google claims that it has never registered as many searches for…
Category : Seo & sem 08-05-2020 by Silvia Mazzetta
First steps into JavaScript – a practical guide 3
After we learned the basic ofaccessing DOM elementsandhow to modify them,we are ready for the more exciting parts – handling DOM events. This allows us to make our web way more interactive, and finally we can put our JS knowledge into practice. User input such as keyboard actions or mouse clicks…
Category : Javascript 07-05-2020 by Iveta Karailievova