Every company is a target.
No industry is safe, or immune to cyber-crime, and although technology in IT security has come a long way, the number of data hacking is growing.
Knowing your potential attacker is essential to being prepared to defend your company from hackers and to protect your data.
According to The Verizon 2013 Data Breach Investigations Report (DBIR), there are 3 types hackers :
Type 1: Activists (aka, Hacktivists) TARGET: Information, Public Sector, and other Service Industries DATA GOAL: To access personal information, credentials and internal data of the organization.
Type 2: Spies TARGET: Manufacturing, Professional Services, and Transportation Industries DATA GOAL: To access credentials, internal data of the organization, and intellectual property.
Type 3: Professional Criminals TARGET: Finance, Retail, and Food Industries DATA GOAL: They want stored credit card information, credentials, and bank account details of customers.
According to the DBIR, the first reason for hacks is financial gain at 75%.
So,your IT security team must act. They must be sure to protect where the relevant assets sits (i.e., POS controller, Database, File Server, Directory Server, Mail Server, etc.) immediately and completely.
Furthermore, most targets are breached by hacks, malware, or both.
We also must be aware that viruses and malware are constantly evolving, making it difficult for anti-ware to stay relevant fast enough to detect, alert, and/or destroy in time.
In addition, log-analysis and SIEMs have serious blind-spots, since not all applications have internal logging mechanisms. If an app is not being logged, your log-recording system is as good as nothing.
These issues should not and cannot be ignored. Educate yourselves immediately, so that you may reinforce your IT security with the best tools possible, and prevent intruders from taking advantage of your weaknesses.
original source: business2community

Janeth Kent
Licenciada en Bellas Artes y programadora por pasión. Cuando tengo un rato retoco fotos, edito vídeos y diseño cosas. El resto del tiempo escribo en MA-NO WEB DESIGN AND DEVELOPMENT.
Related Posts
Android Hidden Codes: unveiling custom dialer codes and their functionality
In the world of Android smartphones, there exist numerous hidden codes that can unlock a treasure trove of functionalities and features. These codes, known as custom dialer codes, provide access…
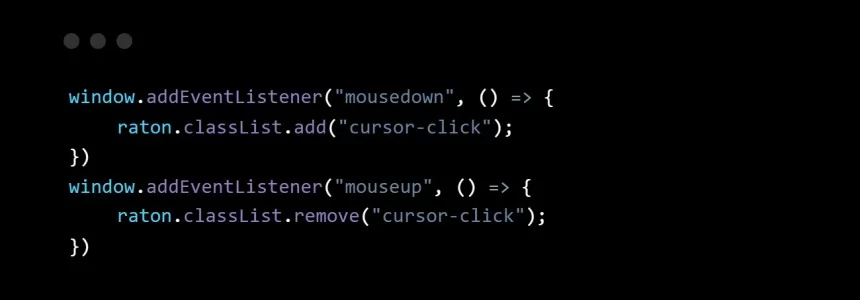
How to make your own custom cursor for your website
When I started browsing different and original websites to learn from them, one of the first things that caught my attention was that some of them had their own cursors,…
8 benefits of having a website for your business
At this moment, the Internet is a phenomenon that is sweeping the world. It has been able to interconnect millions of users all over the planet. People have made the…
Open source web design tools alternatives
There are many prototyping tools, user interface design tools or vector graphics applications. But most of them are paid or closed source. So here I will show you several open…
How to create a .onion domain for your website
The dark web, a hidden network accessed through the Tor browser, offers enhanced privacy and anonymity for websites. To establish a presence on the dark web, you can create a…
The ultimate cybersecurity checklist for programmers
In today's digital age, cybersecurity has become an essential concern for programmers. With cyber threats on the rise, it is crucial for programmers to adopt robust security practices to protect…
How to access webcam and grab an image using HTML5 and Javascript
We often use webcams to broadcast video in real time via our computer. This broadcast can be viewed, saved and even shared via the Internet. As a rule, we need…
How to Send Email from an HTML Contact Form
In today’s article we will write about how to make a working form that upon hitting that submit button will be functional and send the email (to you as a…
Network attacks and how to avoid them
Nowadays it is impossible to list all the different types of attacks that can be carried out on a network, as in the world of security this varies continuously. We…
How to multiply matrices in JavaScript
It may seem strange to want to know how to multiply matrices in JavaScript. But we will see some examples where it is useful to know how to perform this…
JavaScript Formatting Date Tips
Something that seems simple as the treatment of dates can become complex if we don't take into account how to treat them when presenting them to the user. That is…
Top tools for UX design and research
This article is a compilation of the "ux tools" I have tested in recent years. I've separated the tools by categories, although I recommend you to take a look at all…